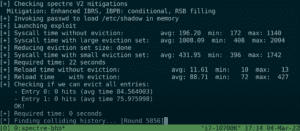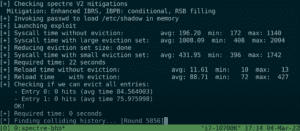
VUSec finds new Spectre-v2 vulnerability in Intel and Arm CPUs
Security researchers at the Vrije Universiteit Amsterdam (VUSec) found a vulnerability in most Intel CPUs. The team managed to leak kernel memory in modern Intel CPUs as unprivileged users.
Intel and Arm have been taking hardware measures to counter Spectre attacks since 2018. Spectre-v2, the se... Read more

Three critical vulnerabilities discovered in APC Smart-UPS devices
UPS flaws allow for remote code execution and remote fire-based interruptions
Security researchers at Armis have detailed a trio of vulnerabilities in so-called Smart-UPS devices sold by Schneider Electric subsidiary APC. These flaws allow for unnoticeable remote code execution, replacing of fir... Read more

Microsoft patches important vulnerability for Exchange Server
Microsoft patched an important vulnerability in Microsoft Exchange Server during Patch Tuesday. In addition, 70 other issues were addressed.
CVE-2022-23277 allowed cybercriminals to remotely activate malicious code via a network call to a server account. Ultimately, lateral moves allowed hackers... Read more
CyberRes introduces GTAP+, threat intelligence for CyberRes Galaxy
CyberRes introduces the Galaxy Threat Acceleration Program (GTAP+) for its CyberRes Galaxy security platform.
GTAP+ provides end users of ArcSight Enterprise Security Manager with the latest threat intelligence. Moreover, the service informs on context to help customers better understand threats... Read more
Major tech companies provide free cybersecurity to US industry
Cloudflare, CrowdStrike and Ping Identity established the joint Critical Infrastructure Defense Project to protect companies in strategic US industries free of charge.
According to Cloudflare, CrowdStrike and Ping Identity, it's imperative for vendors to defend vulnerable industry sectors agains... Read more

Linux affected by critical Dirty Pipe vulnerability
Researchers from CM4all discovered that the Linux kernel was hit by Dirty Pipe, a vulnerability that allows hackers to inject malicious code into root processes.
According to CM4all researchers, the vulnerability allows hackers to overwrite data with malicious code in read-only files. Injecting ... Read more
‘Google and Microsoft bidding against each other to acquire Mandiant’
Google and Microsoft are said to have set their sights on Mandiant. The tech giants hope to realize the acquisition to boost their cybersecurity portfolio.
A source from The Information claims that both Google and Microsoft have shown interest in Mandiant due to a great demand for its security s... Read more
Critical Microsoft Azure bug allowed customers to breach accounts
A vulnerability in Azure Automation put the data of entire Azure environments at risk. Today, Microsoft announced that the problem has been patched behind closed doors.
Microsoft Azure Automation is used for process automation and update management. The service allows customers to schedule vario... Read more

Fraud detective Friss acquires Polonious
Friss, a fraud detection specialist, is acquiring Polonious.
Friss develops fraud detection and prevention software. Insurers use the technology to calculate risks and prevent fraud. Today, Friss announced the acquisition of Polonious. Polonious develops fraud investigation and case management s... Read more
Nvidia data breach by Lapsus$ is actively exploited
A data breach at Nvidia allows cybercriminals to disguise malware with trusted code signing certificates.
Since last week, ransomware group Lapsus$ claims to possess over 1TB of private Nvidia data. Although Nvidia acknowledges that data was stolen, the organization "expected no impact on custom... Read more