Microsoft reveals high prices for extended support for Windows 10
Windows 10 will no longer receive free security updates starting Oct. 14, 2025. Microsoft therefore recommends that users switch to Windows 11 before that date. If not, safe continued usage will only be possible through the Extended Security Updates program. That comes at a high cost.
Microsoft ... Read more

‘Cascade of errors’ enabled Chinese infiltration at Microsoft
Chinese hacker group Storm-0558's attack on Microsoft in 2023 should never have happened. That is the conclusion of the U.S. Cyber Safety Review Board (CSRB). In the report, the CSRB describes a host of security flaws that made the infiltration possible.
Microsoft, aside from being active in a w... Read more

xz backdoor shows how vulnerable open-source is to hackers playing the long game
A security leak in the Linux compression tool xz shows open-source systems' vulnerability to multi-year infiltration tactics by "trusted" contributors. In this case, the culprits added malicious code after the original creator appeared to neglect the project. A competent successor was supposedly re... Read more

Google patches critical Android vulnerability for devices with Qualcomm chipsets
Google closed 28 leaks during the April Android patch cycle, including one critical one. This leak makes phones with Qualcomm chipsets susceptible to remote attacks. Another high-priority vulnerability is in Android's own code, which allows malicious apps to increase their permissions without user ... Read more

Temporarily no new users welcome on PyPi due to malware
The Python repository felt compelled to intervene after packages were uploaded that executed malicious code on devices. It was also temporarily unable to create new projects.
PyPi has since returned to normal operation. However, it was not possible to register and create projects for 10 hours. G... Read more

Large-scale attack on Ray framework exposes AI security risks
For seven months, attackers had free reign to wreak havoc inside the AI infrastructure of major tech companies. An exploitation of vulnerability CVE-2023-48022 in the widely used open-source Ray framework has led to manipulated models, stolen hardware cycles and compromised data. Its developer Anys... Read more
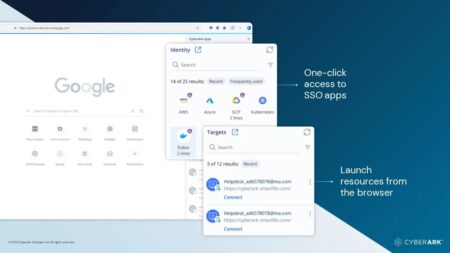
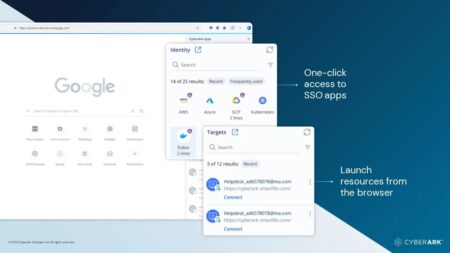
CyberArk launches Secure Browser for secure access
With the CyberArk Secure Browser, companies can build additional security and privacy safeguards into employee browser sessions.
CyberArk has experience in privileged access management. This allows employees' and partners' access rights to applications to be controlled so that only authorized us... Read more

Fortinet integrates FortiGuard SOCaaS with Security Fabric
Companies that have outsourced SOC operations through FortiGuard SOCaaS can now integrate Fortinet solutions (local or cloud-based) through the Security Fabric. This further streamlines mitigation processes for network environments.
Users of the managed FortiGuard SOCaaS service can now integrat... Read more

CrowdStrike Falcon XDR now integrates with Rubrik Security Cloud
CrowdStrike and Rubrik have announced a strategic partnership. Customers can now combine CrowdStrike's XDR platform with Rubrik Security Cloud, allowing security teams to better protect sensitive data.
Both parties state that IT environments today are highly complex, requiring defenses against c... Read more

Number of exploited zero-days up more than 50%
Figures from Google show that last year there were 97 actively exploited zero-day vulnerabilities. In 2022, the number was still 62 vulnerabilities.
With this, the upward trend has returned. A year ago, the figures still showed a positive trend downward. According to Google data, the year 2021 m... Read more