New security vendor in our region promises insight into the vulnerability of all conceivable assets within the organization and does this in a user-friendly and simple way.
If you really want to tackle security properly, you must first know what you have in terms of assets, and what these assets are up to. After all, if you don’t know you have an asset in the network that is vulnerable, you can’t do anything about it either. At Armis Security they came up with the plan years ago to provide broad and deep visibility into the assets of organizations by capturing all of the traffic from all of the assets of an organization. So that something like that wouldn’t be possible anymore. We spoke with Patrick de Vries and André Heller, Strategic Account Executive and Solution Architect respectively at Armis Security, to get to know more about the company.
Well kept secret (in our region)
When we call Armis a new security vendor, you might think that this is a very young start-up. However, nothing could be further from the truth. Armis Security has been around since 2015/2016. Like many other security companies, it was founded in Israel over the last decade, but moved to Palo Alto, California, fairly quickly. There are some big investors behind it, such as Insight and Capital G. As recently as last November, it raised over $300 million in an investment round. This has resulted in a market value of no less than $3.4 billion.
All in all, we can safely call Armis Security a pretty established and very serious player. The fact that we are not yet familiar with the company here is mainly due to the fact that it only took the step outside the US about two years ago. It then followed the ‘traditional’ route: first the UK, then France and DACH. Now it’s the turn of the Benelux and the Nordics. According to De Vries, the way in which Armis Security does this kind of expansion says a lot about how serious they are about it. In fact, a team is always immediately put in place in a new region. It does not start with a single person who has to cope on his own for a while. He expects to have a team of four or five people in our region soon.
Straightforward pitch
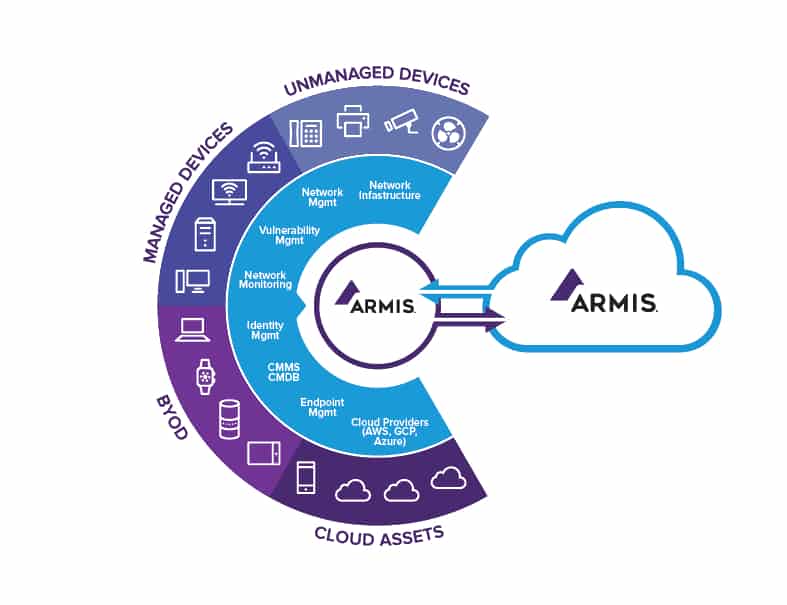
Armis Security’s pitch is not that terribly complicated. The company’s goal is to provide customers with a solution that allows them to make all devices in the network visible. Note that this is not a subset of products, but anything you can think of. IT devices, OT devices, IoT devices, wired, wireless, managed, unmanaged, all traffic can be captured. These can be traditional IT devices, but also, for example, industrial or medical.
Armis Security also promises that the collection of data and insights from assets takes place in a very accessible way. It happens passively and agentless, with the help of a so-called collector. This is a piece of hardware, but it can also run in a virtual environment. A customer does not have to install agents and the collector does not actively scan the network. This is a good thing of course, because on many IoT devices you can’t install an agent at all. The collector simply captures everything that happens on the network and displays this information in a dashboard. This takes place via SPAN (Switch Port Analyzer), or mirroring.
How many and which type of collectors an organization needs depends on all sorts of factors, Heller explains. One example is the number of locations. In principle, you need at least one collector per site. The size of this collector in turn depends on how large the branch is. You can also choose to reduce the number of collectors to be purchased by virtualizing part of them, of course. Heller indicates that their largest customer currently has more than 1000 collectors. This indicates that Armis Security’s platform scales well. It has to, because Armis Security primarily focuses on large organizations with 800 employees or more.
Cloud takes center stage
Based on the description above of the collector you connect to a switch, you might think that Armis Security’s platform is an on-premises offering. That is not true, however, we learn from De Vries. The cloud plays a crucial role in the offering. This distinguishes Armis Security from other vendors operating in the same market. It has put all metadata (of devices/equipment) in the cloud from the beginning. This knowledge base connects to the collector, which you connect to a core switch in the organization. The fact that Armis Security uses the cloud for a substantial part of its offering also makes the service it provides very easy to purchase. Literally the only thing you have to do is plug in the collector or collectors, configure ports and you’re ready to go.
The knowledge base in the cloud is the heart of the Armis Security solution. This database now contains three billion devices and thirteen million device profiles, says Heller. That’s a lot, but it doesn’t mean that it contains all of the devices out there. If you connect a new device in your network, the platform deals with this without much problems, he indicates. As soon as the Mac address comes in, it is already clear which brand it is, who manufactured it and who sold it. If that is Philips, for example, then the chances are already fairly good that it is a medical device. If in the end it is still not clear what it is, Armis Security has a team dedicated to finding out which device it is.
The knowledge base in the cloud is a very important source of information for Armis Security’s solution. It also uses data gathered from real-time inspection of traffic. With this, you can see what is actually happening on the network and with all the assets at any given time. Armis Security stores these events, and keeps them for 90 days. The so-called inventory page, the page that shows which devices were found, remains available forever. Even if you remove a device from the network.
Deep insights
As we always do when we speak to a new vendor for the first time, we asked Armis Security for a demo of their platform. We do this to get a good impression of what the solution looks like and of what it can do.
To us, it was immediately clear that you can really go very deep into the activity of a device. Not only can you see when something received an ip address and what ip address is, or when it is connected or disconnected. Armis Security also makes the flow of connections transparent. That is, if the behavior of a device changes and the sequence of processes is different than usual, the solution gives an alert. These alerts are bundled, by the way, so that a security team doesn’t get lost in them. You can also see, for example, whether a PC on the network has an endpoint security solution running or not.
Armis Security can’t gather the same information from all types of devices, by the way. It all depends on the type of device, and what that device has to offer in terms of insights and information. On many OT devices this will be less than on devices that can run software. It also depends on third-party integrations. If these are available, Armis Security will have access to much more information than if these aren’t. There are integrations with Microsoft, CrowdStrike and Qualys, for example.
Asset management as a bonus feature
When it comes to OT devices, there’s one other interesting characteristic that can help Armis Security. Most of the data coming to and from these is not encrypted. That means that Armis Security can just ‘read along’ with commands, for example. You get a very granular view of the write commands to PLCs in this way. That in turn gives additional insights into the security status of that device.
The insights you can gain through Armis Security go beyond cybersecurity vulnerabilities, Heller notes at this point of our conversation. For medical devices, for example, Armis Security also adds any FDA recalls to the dashboard. The same holds for MDS2 files, in which medical equipment manufacturers disclose how the equipment performs in terms of security and privacy. For the sake of completeness, MDS2 stands for Manufacturer Disclosure Statement for Medical Device Security.
Armis Security also sees which body part a CT scanner scans at any given time. That enables hospitals to do some asset management. That is, they can use this data to optimize the use of the device. Armis Security also still detects cyber security threats for this type of equipment, Heller quickly adds. For example, they showed how WannaCry was present on a CT scanner and moved laterally through the hospital.
Own query language
In addition to the deep insights, something else caught our eye during the demo. Armis Security has developed its own query language, ASQ. This allows you to search relatively easily through the huge pool of data that large organizations generate. You can work with the front end of this language almost entirely by mouse. That means that you don’t have to enter complex queries. You simply click the things you want to see, and the dashboard displays them. You can also filter easily. For example, if you do not want to see results from devices in the corporate network, then you can filter those out.
The dashboard does not make use of NLP, where you ask a question in a text box in a normal human sentence and get an answer. You still have to really know what you are looking for, because you have to make a selection with the mouse at each step. This is not a problem in itself, since these dashboards are different from those of BI platforms, where you do encounter NLP a lot. Those need to be used by as many layers within an organization as possible, which is much less the case with Armis Security. A manager without security responsibilities, for example, probably won’t need to work with an Armis Security dashboard anyway.
Actionable detections
So far, we have established that Armis Security’s platform detects almost everything that happens in a network and presents these findings in a clear dashboard. Of course you can configure it to send notifications or add tags, so that an incident can be dealt with as quickly and easily as possible. All this happens in real time, not just at a specific moment, Heller emphasizes again at this point.
Getting alerts is a good first step on the way to ensuring that a threat can be averted. However, with the Armis Security platform you can also automate your responses. That is, it is possible to take automated action if the platform detects something. Armis does not do this itself, but with the help of integrations with third parties. An organization must use the software and/or hardware of those third parties in order for this to be possible, but that goes without saying. You can use policies you create yourself, but also crowd sourced policies.
These policies can be as detailed as you want, by the way. You don’t have to disable a device completely, for example. It is possible to only disconnect the network connection, but keep the device itself in operation. In the medical world, for example, that is a good thing. A hospital can continue to use equipment offline while the security problem is solved in the background.
Armis Security continues to develop
Armis Security’s platform may already be very comprehensive, there is always room for improvement. When we ask Heller at the end of our conversation about whether multi-tenancy is also part of the platform, he says that Armis does not offer this at the moment. However, they are working on it behind the scenes. For large organizations with their own security team that monitors, manages and executes everything centrally, multi-tenancy is not very interesting. If Armis Security also wants to enter the market more broadly via MSSPs, then multi-tenancy is a crucial feature to add. This is something that will happen in the (near) future.
Conclusion
Listening to De Vries and Heller, Armis Security’s solution is already pretty mature. This is clear from the enormous number of devices that the company already has in its knowledge base and is constantly adding to it. It is also a modern solution, with subscription model per employee or per location/site to go with it. This is the same for all organizations, except for the education sector. Armis Security offers it to that sector for half the price. The focus from Armis Security on ease of use is also modern, and always does well, if a vendor can prove it of course. From what we’ve seen, Armis can prove that.
When it comes to subscription, customers can choose from multiple variants. You can go for only the visibility piece or also include the module for taking actions. That’s smart, because organizations usually already have made considerable investments in cybersecurity and may have already taken care of the actions part in other solutions. However, if you want to Armis Security’s platform as a launching pad for these actions, you can do that by means of the integrations. This way, the solution basically fits into any environment and can also be integrated into it almost seamlessly.
TIP: In addition to Armis Security there are other, until recently less well-known names in the security world. Two of them are Noname Security and Salt Security. Yet both providers of API Security solutions achieved unicorn status late last year. Follow the links to read our articles on these security vendors.
