The A- and M-Series of processors for Apple’s mobile devices and PCs contain a vulnerability that allows hackers to easily tap sensitive data.
This was discovered by researchers from American and German universities. The researchers call the vulnerability iLeakage. It is a side-channel vulnerability that allows sensitive information to be tapped from the A- and M-Series of Apple processors. This is information that becomes visible by tapping clues left in electromagnetic radiation, data caches and other manifestations within an affected system.
The aforementioned side-channel that can be accessed with the vulnerability, in this case, is speculative execution. This is a performance enhancement found in modern processors.
Test results
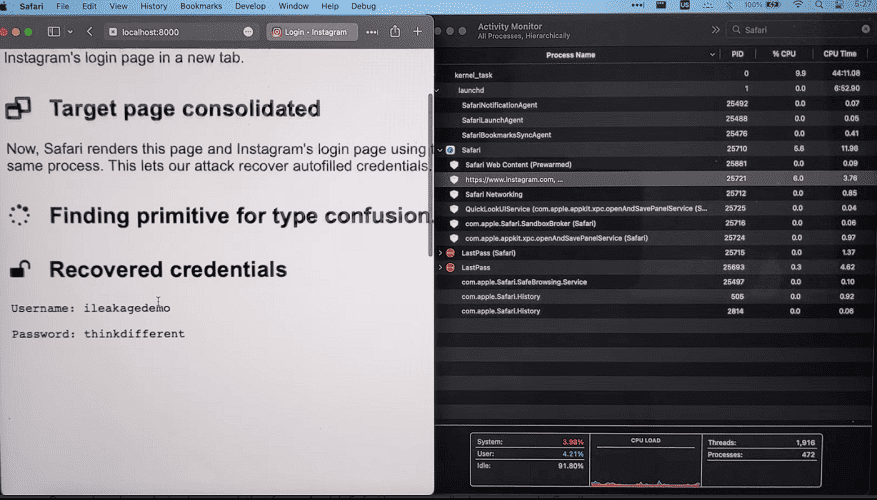
The researchers set up a specific website in their test environment for testing the iLeakage vulnerability. They then accessed this website with vulnerable Apple iOS and macOS systems. A JavaScript on the site caused the side-channel to open and pass information to the hackers.
Within five minutes, the rogue website managed to profile the target machine. It then took another half minute to pull out a 512-bit secret, such as a 64-character character string. With this, they eventually managed to easily retrieve a YouTube watch history and the contents of a Gmail inbox.
However, to do this, the target must have logged into these services and had the auto-fill password enabled. All the information could be viewed simply in the Safari browser of an Apple device.
For the vulnerability, the main flaw would be in the WebKit browser engine. Apple is aware of the vulnerability and says a patch will follow in an upcoming update. Whether the vulnerability is already being actively exploited is unknown.
Same discoverers Spectre and Meltdown
The side-channel vulnerability in Apple processors evokes a comparison to the earlier Spectre and Meltdown vulnerabilities discovered by the same researchers in 2018. In these, Intel processors and, to a lesser extent, AMD processors were mostly affected. As a result, a lot of fixes have since been affected.
Also read: Investigators find seven new Meltdown and Spectre attacks