
Microsoft Azure Local, 365 Local generally available: the cloud, offline
The possibilities for running Azure in a private environment are becoming much greater. With the general avai...

The possibilities for running Azure in a private environment are becoming much greater. With the general avai...
There is a lot going on around privacy and compliance, especially in Europe. This in itself is a good thing, because data should be adequately protected, especially if it concerns personal data. In practice, however, it turns out to be quite disappointing how well organizations do this. We read and write a lot about data breaches. Over the years there seem to be more rather than fewer of them. Is that because organizations don’t want to do better or can’t do better? Whatever the reason, a good policy on privacy and compliance is indispensable in the current era. Especially with all kinds of new legislation that has been introduced and is coming, the need to put this high on the agenda is only increasing.

National security concerns scuttled the proposed deal. Zoom and Five9 have mutually terminated the merger ...

Agreements cover computer chip supplies and general rules for technology trade. The United States and Euro...

The Google Docs web client is in the process of adding support for their background watermarks and expanding ...

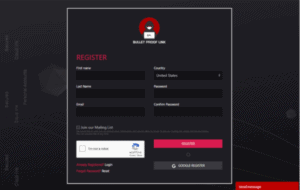
Picture for a moment a scenario where you have as many attempts as you want to get a username and password ri...

The EC has accused Google of illegal practices on Android devices to enhance the dominant position of their s...

In a statement highlighting concerns about China’s growing power, the EU’s trade and digital chiefs said ...

Google is going to court this week in an attempt to reverse a monumental $5 billion European Union fine impos...

Michael Dell, the CEO of Dell, said Dell is not longer on an acquisition strategy. Dell ruled out any major f...

The United States and European Union plan to take a more unified approach to limit the market power wielded b...
Microsoft announced they catched an extensive phishing-as-a-service operation providing various services to ...