Everything there is to find on tag: cloud environments.

Top story
Everything there is to find on tag: cloud environments.


Security tools are often no obstacle for hackers due to misconfigured cloud environments. Moreover, misconfig...



New research has come out suggesting that two-thirds of cloud security incidents could have been avoided if t...

Security researchers from Technische Universität Berlin have devised an attack that proves AMD's Secure Encr...
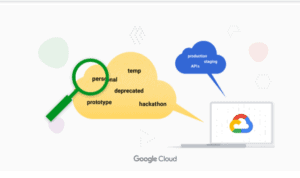
Google announced a new feature of Active assist on August 6. Named Unattended Project Recommender, the featur...