The Monti ransomware gang is active again after a short break and is using a new Linux locker for its attacks. VMware ESXi servers, legal firms and government organizations are being targeted.
Monti, a rebrand of the well-known Conti ransomware gang, has restarted its malicious activities after a two-month break. To do so, the ransomware hackers are using a new Linux locker, Trend Micro researchers discovered.
New locker differs from previous variants
The new Linux locker, Ransom.Linux.MONTI.THGOCBC, shows clear deviations from the previous variants, according to the researchers. Namely, the earlier variants were mainly based on leaked Conti source code, but the new version has a different encryptor. Moreover, this one also exhibits anomalous behaviour.
The researchers indicate that the new locker differs mainly in the way it tries to evade detection. This, they say, makes it more difficult to identify and combat the Monti attacks.
New ransomware functionality
The new Linux Locker includes the removal of the ‘–size,’ ‘–log,’ and ‘-vmlist’ parameters and the addition of a new ‘-type=soft’ parameter. This should stop VMware ESXi servers in a more subtle way. Probably to avoid detection. Also added is a ‘–whitelist’ parameter that instructs the locker to skip special VMware ESXi servers on the host.
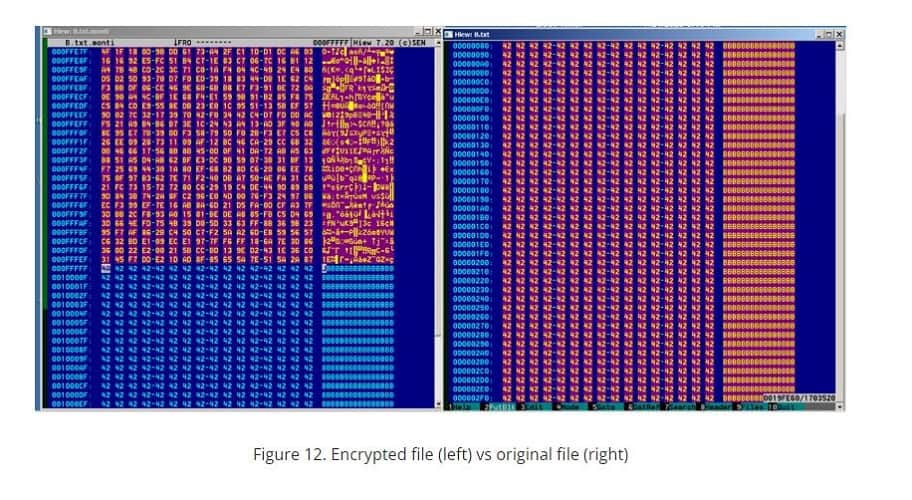
In addition, the locker uses the AES-256-CTR encryption method of the OpenSSL library, among other things. The previous variant used Salsa20 for this purpose. Of files between 1,048 and 4.19 MB, only the first 100,000 bytes are encrypted.
Source: Trend Micro
Files under 1,048 MB are encrypted in their entirety. Of files larger than 4.19 MB, a portion of the content is encrypted. The size of this portion is determined by a Shift Right operation.
Furthermore, encrypted files are given the .MONTI extension and a ransom note is placed in a readme.txt file in each directory to be processed.
In this article, we take a closer look at the motives of hackers to attack VMware ESXi servers: VMware ESXi servers vulnerable to Akira ransomware