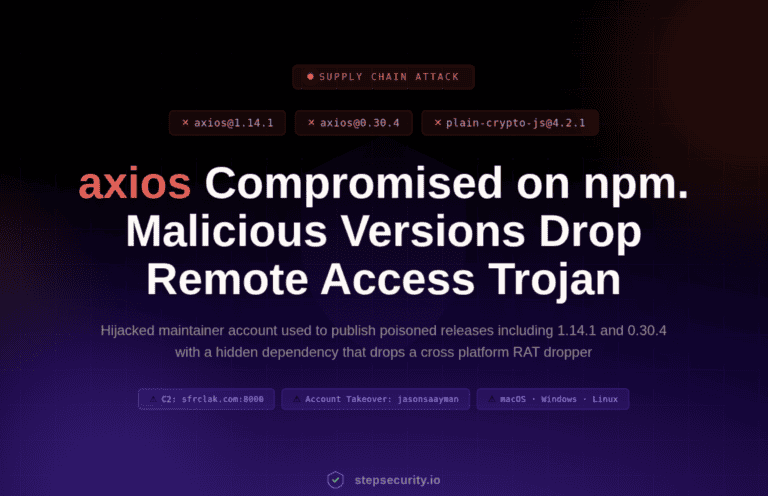
Two versions of the widely used JavaScript library axios were maliciously published on npm on March 31, 2026. A hijacked maintainer account is behind the attack. The compromised versions silently install a cross-platform Remote Access Trojan (RAT) on macOS, Windows, and Linux.
Security firm StepSecurity discovered that axios@1.14.1 and axios@0.30.4 were published via the compromised npm account of jasonsaayman, the primary maintainer of the axios project. The attacker changed the email address of that account to an anonymous ProtonMail address and manually published the infected packages via the npm CLI, completely bypassing the normal GitHub Actions CI/CD process.
Axios has over 300 million weekly downloads and is used in virtually every Node.js and browser project that makes HTTP requests. A compromised version therefore has enormous potential reach. Notably, axios itself does not contain a single line of malicious code.
Fake dependency as an attack vector
The attacker injected an unknown dependency named plain-crypto-js@4.2.1 into both axios versions. This package is neither imported nor used anywhere in the axios source code. In other words: its sole purpose is to execute a post-install script that acts as a RAT dropper. The package does, however, disguise itself as the legitimate crypto-js library, including the same description, author name, and repository URL.
After execution, the dropper script `setup.js` performs three cleanup steps. First, it removes itself; then it deletes the `package.json` file containing the malicious post-install hook; and finally, it replaces that file with a “clean” version. Anyone inspecting node_modules/plain-crypto-js afterward will see a completely innocent-looking package. But the presence of the plain-crypto-js folder in node_modules is sufficient proof that the dropper has been active.
The attack was carefully prepared, according to researchers at Step Security. On March 30 at 07:57 Dutch time, the attacker first published plain-crypto-js@4.2.0, a clean version, purely to build up a publication history. It wasn’t until nearly eighteen hours later that the malicious version 4.2.1 appeared. Both infected axios versions followed within an hour.
RAT Targets macOS, Windows, and Linux
The dropper script checks the operating system and executes a platform-specific attack. On macOS, a RAT binary is stored in /Library/Caches/com.apple.act.mond — a path that deliberately resembles a legitimate Apple system process. On Windows, the malware copies PowerShell to %PROGRAMDATA%wt.exe and executes a hidden PowerShell script. On Linux, it downloads a Python script to /tmp/ld.py. All three payloads communicate with the same command-and-control server at sfrclak.com:8000.
Thus, the threat continues to spread via npm packages. It is, in fact, a repeat of a notorious recent incident. In December, the Shai-Hulud 2.0 worm was found to have stolen some 400,000 developer secrets via infected npm packages, also using post-install scripts for the attack path. And in September, Chalk and Debug had already been compromised following a phishing attack on a maintainer account. So the same tactics were used as in this current Axios attack.
What to do if you installed the infected versions
Anyone who has installed axios@1.14.1 or axios@0.30.4 should assume that their system has been compromised. StepSecurity recommends downgrading to axios@1.14.0 or axios@0.30.3, removing the node_modules/plain-crypto-js directory, and reinstalling with npm install –ignore-scripts. All credentials on affected systems, such as npm tokens, cloud keys, SSH keys, and CI/CD secrets, must be rotated. In CI/CD pipelines, –ignore-scripts is recommended as a standard measure to prevent post-install scripts from running automatically.
StepSecurity confirmed the malware’s operation via runtime analysis using its Harden-Runner tool. A connection to the C2 domain was detected just 1.1 seconds after running `npm install`.