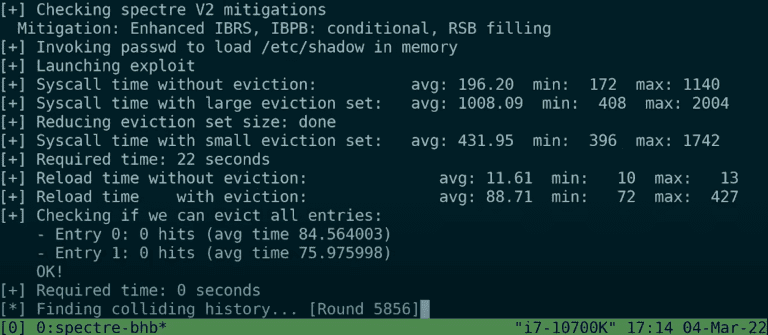
Security researchers at the Vrije Universiteit Amsterdam (VUSec) found a vulnerability in most Intel CPUs. The team managed to leak kernel memory in modern Intel CPUs as unprivileged users.
Intel and Arm have been taking hardware measures to counter Spectre attacks since 2018. Spectre-v2, the second variant of the attack type, was discovered in the same period. Unprivileged users were found to be able to leak the kernel memory of systems with Intel and Arm CPUs. Although Intel and Arm developed two security measures (eIBRS and CSV2), the hole appears to remain unsealed.
VUSec found a new way to perform Spectre-v2 attacks on modern CPUs. The method is known as Branche History Injection.
How does Branch History Injection work?
CSV2 and eIBRS ensure that code is exclusively sent to authorized targets. The processor remembers authorized and unauthorized targets through a global history, similar to memory. VUSec researchers managed to manipulate this global history. By providing incorrect information, CPUs were drilled to send data to unauthorized, vulnerable targets.
Intel and Arm respond
Intel and Arm have been notified. Intel says most of its CPUs are vulnerable. The organization is currently developing an emergency fix.
Arm has 16 vulnerable Cortex CPUs and four vulnerable Neoverse CPUs. The organization responded by detailing five mitigations.