
Kubernetes attack surface explodes: number of threats quadruples
Kubernetes is the industry standard for cloud-native workloads. Its ubiquity invites cyberattackers to exploi...

Kubernetes is the industry standard for cloud-native workloads. Its ubiquity invites cyberattackers to exploi...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

Nextcloud is discontinuing its bug bounty program on HackerOne. The reason is the increasing flood of generic...
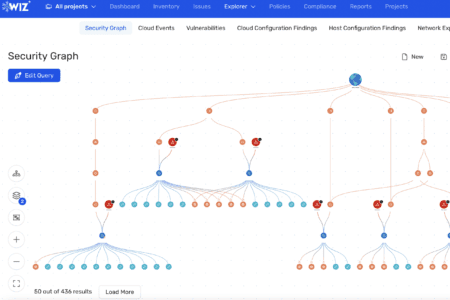
At Google Cloud Next 2026, the message from Google Cloud and Wiz was clear: Wiz is fundamental for how Google...

Arctic Wolf is introducing a new security tool that addresses a well-known problem in cybersecurity: the earl...

Firefox has received the Claude Mythos Preview treatment, leading to fixes for 271 vulnerabilities. As the Mo...

AI development platform Lovable is under fire following reports of a vulnerability that allowed users to acce...

Microsoft has released emergency updates for multiple versions of Windows Server. This follows issues caused ...

Aikido Security is launching Aikido Endpoint, a lightweight agent designed to protect developers’ endpoints...

Kubernetes is the industry standard for cloud-native workloads. Its ubiquity invites cyberattackers to exploi...
A report from Dark Web Informer has raised questions about a possible data breach at Bol.com. On the platform...

Vercel has announced that attackers gained access to internal systems. The attack began at Context.ai, an AI ...