Everything there is to find on tag: malware.
Malware attacks via Excel XLL files rose by nearly 600 percent
Cyber attacks based on Microsoft Excel add-in files (.XLL) increased by nearly 600 percent in 2021. In a new ...
Everything there is to find on tag: malware.
Cyber attacks based on Microsoft Excel add-in files (.XLL) increased by nearly 600 percent in 2021. In a new ...

Researchers have discovered a terrifying new form of malware written from scratch. It is designed to target s...

The attack also targeted non-governmental organizations and IT vendors Microsoft this week admitted that i...
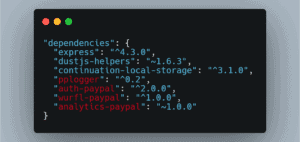
Another 17 malicious packages have been discovered in an open-source repository by researchers. In recent tim...

Researchers say they've found a batch of apps on the Google Play Store downloaded more than 300,000 times bef...
PyPI, the open-source repository used by both large and small organizations to download code libraries, was h...

A new research paper has been published with details about a new technique that can be exploited to inject ma...
The U.S. Homeland Security Secretary says cyber attacks are increasingly posing risks to "public health and s...

"Grifthorse" has already victimized 10 million people worldwide. Security researchers have found a massive...

Akamai Technologies’ acquisition of Guardicore is a move in the right direction and a great way to enhance ...