Researchers at Black Lotus Labs have tracked down a malware variant that has been flying under the radar for two years: AVrecon. The team, part of Lumen Technologies, talks about one of the biggest malware plagues that have targeted SOHO routers.
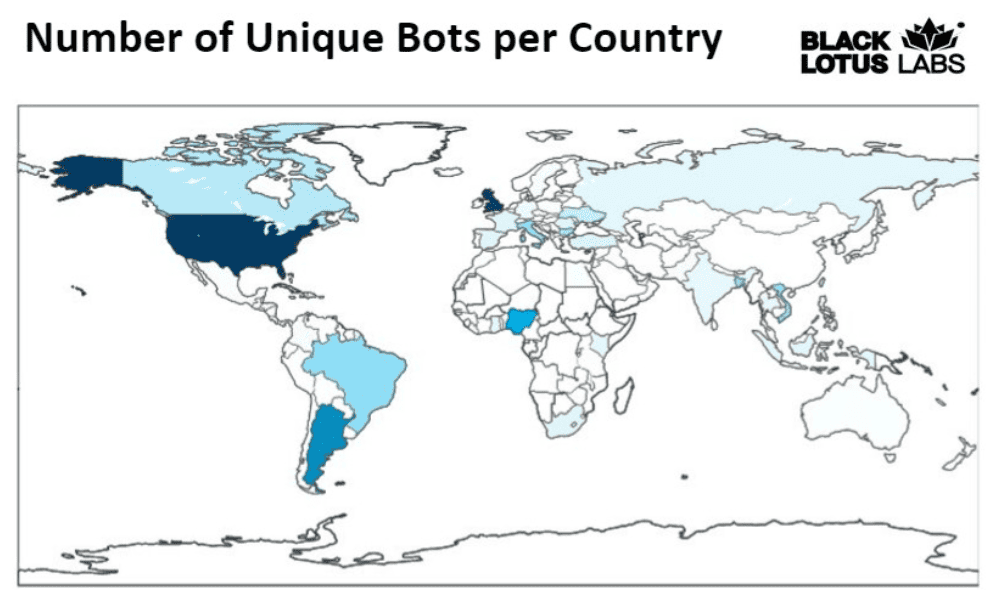
Black Lotus Labs followed AVrecon for 28 days to create a “snapshot” of its activities. Soon, the scale was found to be enormous: 70,000 IP addresses were communicating with the cybercriminals’ command-and-control center. Of those, more than 40,000 were active in the botnet network for more than two days. The targets were SOHO routers, deployed by smaller businesses or home-based individuals. In other words, the IP addresses usually are entirely legitimate.
The malware managed to disguise itself for a long time. This was possible because the criminals did not choose mostly known applications of botnets. Normally, these groups often choose to install a crypto-miner or to carry out DDoS attacks via other people’s networks. However, these catch on rather quickly. Instead, Black Lotus Labs believes the criminals are targeting fraudulent ad clicks and for “password spraying. In the former case, parties such as Google and Facebook are fooled and the criminals generate their income with advertising revenue. In password spraying, the malware searches for crackable cloud services by testing all kinds of passwords.
Vulnerable
A SOHO router is often vulnerable because users do not always update its software and have little insight into what is happening on such a device. We have seen similar exploitations of this blind spot where criminals stole other people’s Internet bandwidth.
Tip: New cybercrime tactic: selling someone else’s Internet connection
Router malware is therefore also in demand: Black Lotus has already detected a variant of it three times in 12 months. As they point out, the rise of remote working is accompanied by a growing range of potential router targets.
Operation
In the blog, the researchers go into depth regarding the exact workings of the malware, although one cannot yet reveal the perpetrators themselves. Once the AVrecon malware enters a network, it first starts searching for its own presence. If AVrecon is already running somewhere, the new entrant destroys itself. It additionally gathers information about the device and network, then sets up a C2 channel that allows it to become part of the global botnet.
The map shows that the botnet operates worldwide, with the U.S. and the U.K. as its center of gravity. This fact, too, will have played a part in the malware flying under the radar. After all, it would have been much more noticeable if it had established itself with these numbers of infections very locally.
Opinion
Those with Lumen Connected Security will now be equipped with protection, according to Black Lotus Labs. However, it states that organizations and individuals should watch for easily cracked passwords, monitor suspicious IPs and keep cloud components from communicating with bots. In addition, it helps to regularly reboot and update the router whenever possible.
Also read: Hackers spread malware in Windows kernel through open-source software