The Python Software Foundation (PSF) has released Python 3.9.2 and 3.8.8 to deal with two well-known security flaws. One of the flaws is remotely exploitable but in practical use can only be used to take a machine offline.
The PSF is urging its users to upgrade systems to Python 3.8.8 or 3.9.2, to address the remote code execution (RCE) vulnerability that is tracked as CVE-2021-3177. The project hastened their efforts to release the update, after users pressured them, concerned about the security flaw.
The Python release team released a statement confirming this.
The team elaborated that since the announcement of the release candidates for 3.9.2 and 3.8.8, they received several inquiries from users, asking them to expedite the final releases because of the security issue.
Users asked
The team says that the inquiries took them by surprise since they believed security content is specifically picked by downstream distributors from source either way and the RC releases give installers for anyone interested in updating in the meantime.
The PSF team continues to say that it turns out the release candidates are mostly invisible to users and in many cases are unusable because of upgrade processes that users already have in place.
The issues
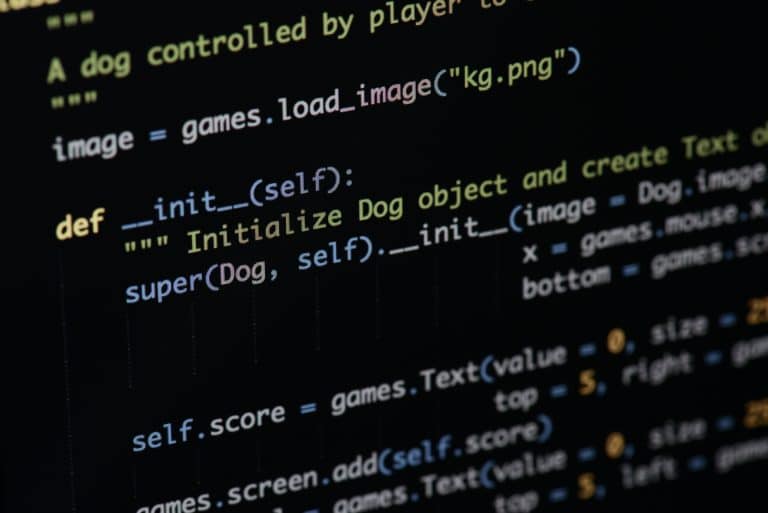
Beginning with Python 3.x to 3.9.1, there’s a buffer overflow in PyCArg-repr in ctypes/callproc.c, which could lead to RCE. This affects Python apps that affect floating-point numbers as untrusted input, as shown by a 1e3000 argument to c-double.from.param.
The bug manifests when “sprint” is unsafely used. The impact is wide since Python is pre-installed for several Linux distribution and Windows 10.
Some Linux distributions like Debian, have been backporting the security parches to shield the built-in version of Python.