Cybercriminals put stolen login data from large companies up for sale in late January. The data came from a number of the companies’ Asian data centers.
This was discovered by security specialist Resecurity in an investigation ongoing since September 2021. According to the investigation, several data center providers, cloud service providers and MSPs in Asia have been affected by a sustained cyber attack. The cybercriminals, originating from China and some other Asian countries, set out to steal login credentials and other sensitive data from (large) customers.
Bloomberg writes that the affected data center providers are Shanghai-based GDS Holdings and Singapore-based ST Telemedia Global Datacenters. Companies from which login credentials and data were allegedly stolen include Alibaba, Amazon, Apple, BMW, Goldman Sachs, Huawei, Microsoft and Walmart.
Multi-year attacks
The attacks have a long evolution, Resecurity’s security experts discovered. The first malicious cyber activities were spotted in September 2021. During this first attack, the cybercriminals managed to get their hands on a list of CCTV cameras, followed by login credentials of operational employees of the data centers themselves and employees of customers operating in the data centers. In addition, they got their hands on data about services purchased and equipment deployed. In addition, they showed interest is the availability of a “remote hands service (RHS) that allows customers to remotely manage their servers in the data center and troubleshoot problems before that.
In the second wave of attacks, carried out throughout 2022, the cybercriminals again managed to steal a customer database with more than a thousand records at a Singapore data center company. This attack, however, was detected and eventually repelled.
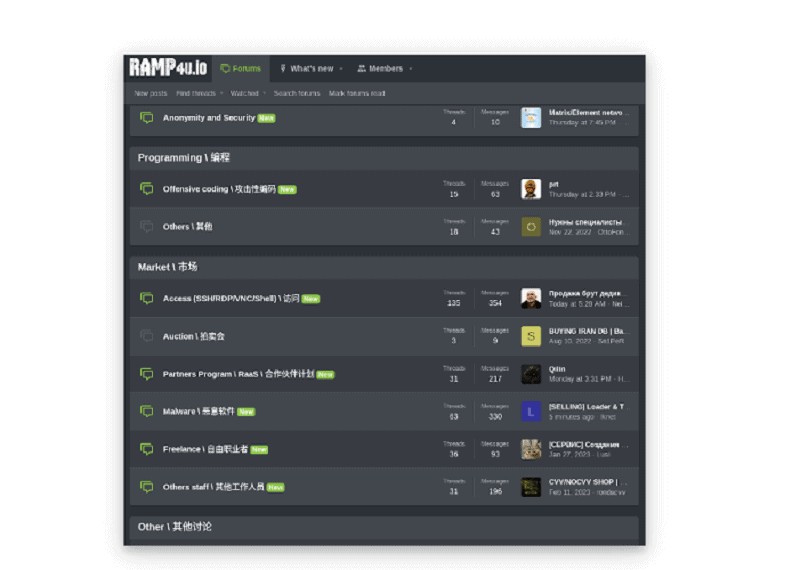
The third and, for now, final episode of this attack occurred recently. Investigators discovered that the cybercriminals put the stolen login credentials and other data of major customers of the affected data center companies up for sale on the dark web. More specifically, this involves the RAMP platform that is mostly used by Initial Access Brokers (IABs) and ransomware criminals.
Also read: European companies plan to increase IT security budget over next three years
Impact unknown
The researchers say they cannot estimate the impact of this large-scale theft of login credentials and other data. By going public now about these attacks on the aforementioned data center providers, they hope to mitigate any impact, but also to create more awareness of this type of attack. Meanwhile, in addition to the affected companies, several CERTs of the affected countries have also been informed about the attack.
