IBM Security X-Force has released its annual Threat Intelligence Index report, which reveals that while ransomware’s share of incidents has declined slightly, defenders were more successful in detecting and preventing ransomware.
According to the report, deploying backdoors that allow remote access to systems emerged as the top action undertaken by attackers last year, with about two-thirds of backdoor cases related to ransomware attempts.
However, defenders could detect the backdoor before the ransomware was deployed, which partially explains the uptick in backdoor deployments due to their high market value.
Ransomware extortion has the highest impact
Charles Henderson, Head of IBM Security X-Force, explained that “The shift toward detection and response has allowed defenders to disrupt adversaries earlier in the attack chain – tempering ransomware’s progression in the short term, but it’s only a matter of time before today’s backdoor problem becomes tomorrow’s ransomware crisis. Attackers always find new ways to evade detection.”
The report also found that the most common impact from cyberattacks in 2022 was extortion, primarily achieved through ransomware or business email compromise attacks, with Europe being the most targeted region.
Cybercriminals were found to be weaponizing email conversations, with thread hijacking seeing a significant rise in 2022. The report also details how cybercriminals often target the most vulnerable industries, businesses, and regions with extortion schemes, applying psychological pressure to force victims to pay.
Manufacturing was the most extorted industry in 2022
Since they’re an attractive target for extortion, manufacturers saw a second year as the most extorted industry, given their low downtime tolerance.
Lastly, the report notes how ransomware operators have made stolen data more accessible to downstream victims, increasing pressure on the breached organization by bringing customers and business partners into the mix.
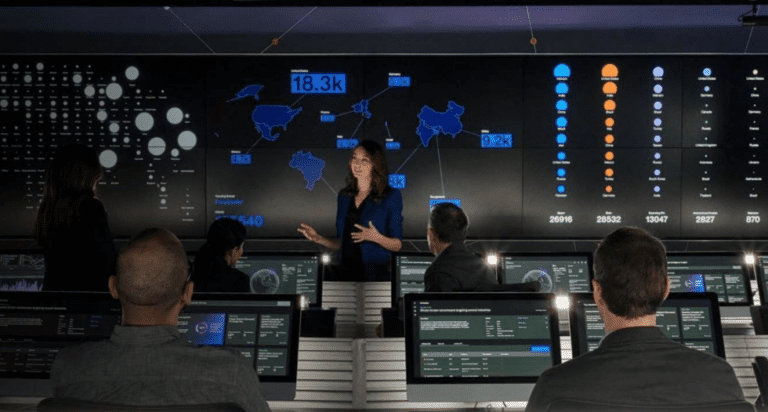
The IBM Security X-Force Threat Intelligence Index report is compiled by pulling from billions of data points from network and endpoint devices, incident response engagements, and other sources. It tracks new and existing trends and attack patterns, and it provides valuable information for individuals and organizations to stay ahead of cyber threat.
Also read: Ransomware fatal for SMBs: security increasingly taken more seriously