The latest vulnerability in Atlassian Confluence Server is already being massively exploited, security experts discovered. It is important to install the patch fast.
CVE-2023-22518, a vulnerability in the Atlassian Confluence Server, is being massively exploited. Several security specialists report this.
According to specialist GreyNoise, these attacks have in common that the IP addresses they work with all target Ukraine. According to the DFIR Report specialists, among the attackers there are also hacker groups trying to carry out a ransomware attack with this. Among them was discovered an attempt by a ransomware group calling itself C3RB3R. In turn, Rapid7 experts discovered ransomware attacks by Cerber ransomware.
Recently disclosed
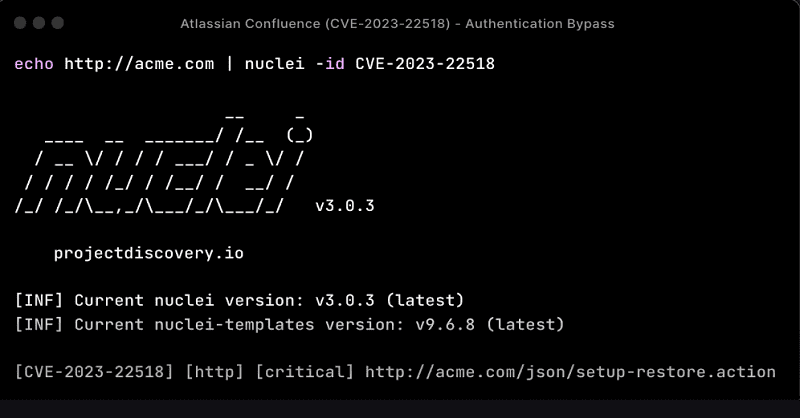
The vulnerability was disclosed by Atlassian last week. This authorization vulnerability targets Internet-connected (on-premises) Confluence servers. It allows hackers to send specially customized requests to these servers to restore endpoint settings.
This can lead to a lot of data loss in the event of an exploit, according to Atlassian. Therefore, timely patching of Confluence instances is critical. Confluence Server accounts hosted in the Atlassian cloud environment were not affected.
Not the first time
This is not the first time the workflow and collaboration specialist has been affected by a critical vulnerability in its Confluence software. In early October, another critical vulnerability was discovered, which hackers also quickly exploited. It took some time before patches were installed by users of the software.