Critical vulnerabilities in WordPress tend to linger. Some website and plugin developers aren’t patching fast enough, says WordPress security specialist Patchstack in a recent report.
A survey by Patchstack shows that the number of WordPress vulnerabilities increased by as much as 150 percent in 2021. To date, 29 percent of these vulnerabilities are yet to receive an update. Patchstack researchers are concerned, as 43.2 percent of all websites run on WordPress.
Overall, 3.4 percent of the vulnerabilities found were critical. 18 percent of the vulnerabilities were major. The vast majority were labelled a medium risk.
Nearly half of all websites are vulnerable
The researchers indicate that approximately 42 percent of all WordPress websites now have at least one vulnerable component relative to the average 18 themes or plugins installed.
Furthermore, six of the 18 components are outdated and therefore more vulnerable. Most vulnerabilities were found in themes and plugins. The number of vulnerabilities in WordPress’ core made up roughly 0.5 percent.
Free plugins
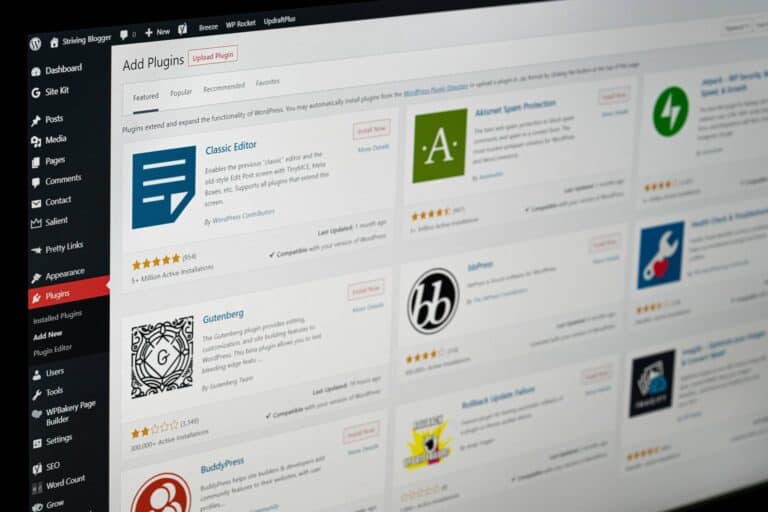
The security specialists found 91 percent of the vulnerabilities in free plugins. Paid and premium add-ons were responsible for 9 percent. Patchstack reasons that the difference is due to better code review and proper testing procedures for paid plugins.
The study also shows that vulnerabilities affect multiple WordPress themes or plugins. The five major theme vulnerabilities affected 55 WordPress themes. The two most critical plugin vulnerabilities affected as many as four million websites.
In the past year, the most frequently found vulnerabilities concerned cross-site scripting (XSS), followed by cross-site request forgery, SQL injections, and arbitrary file uploads.
Work to be done
Patchstack researchers conclude that there’s work to be done in the security of WordPress environments. Patchstack advises users to utilise paid plugins over free plugins, limit the number of add-ons and patching themes and plugins when possible.