International hotel chain InterContinental Hotels Group (IHG) was hit by a cyberattack that has taken down its entire booking system.
In a statement to the London Stock Exchange, IHG reveals it’s dealing with a major global outage. The hotel chain’s mobile apps are currently offline. The outage was caused by “unauthorized activity”, more commonly known as a cyberattack.
Cause unclear
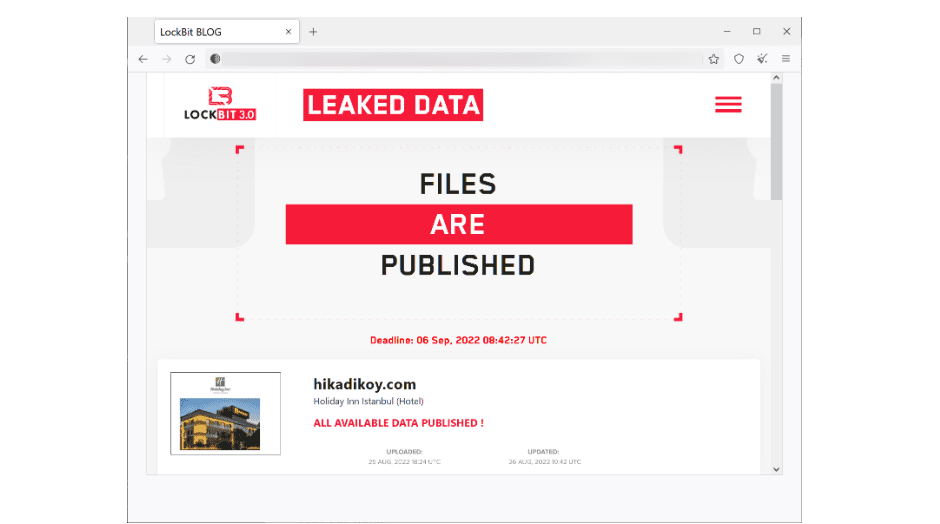
The cause of the attack was not disclosed. IHG says it’s busy restoring affected systems, which indicates the possibility of ransomware. Last month, ransomware group LockBit claimed a successful attack on a Holiday Inn division of IHG in Istanbul.
Recovery efforts
The hotel chain says that it’s cooperating with third-party experts and technology providers to recover the systems. Furthermore, the relevant authorities were notified of the attack.
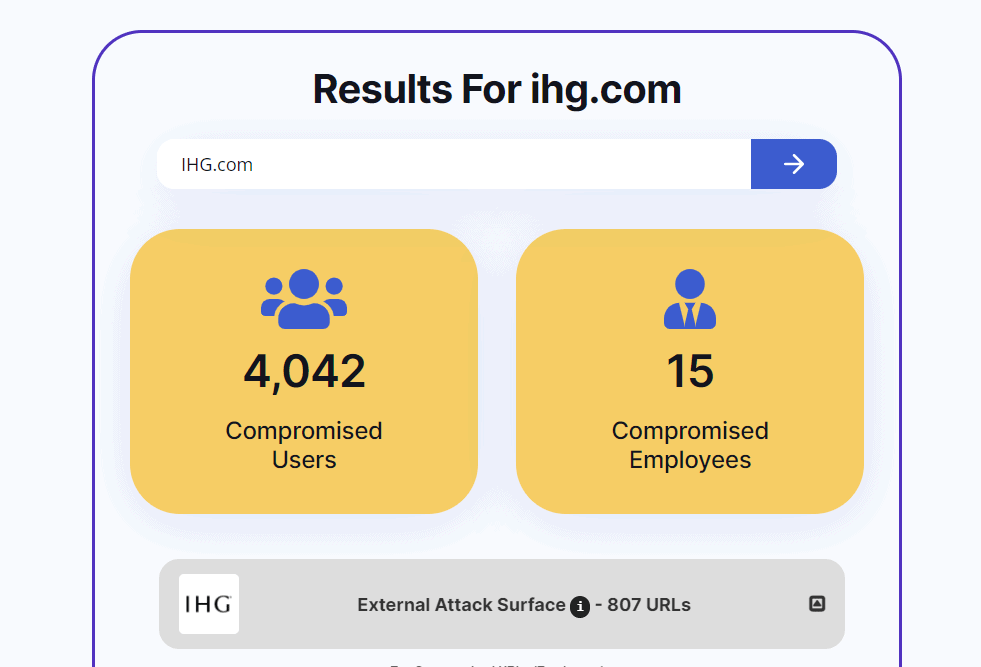
Research by security firm Hudson Rock indicates the attack leaked the login data of 15 employees. Furthermore, the login details of 4,042 IHG users were reportedly breached. Hudson Rock says the number of compromised URLs totals 807.