
Is 46% of your AI-generated code vulnerable?
As AI coding assistants become ubiquitous in enterprise development, a concerning statistic has emerged: 46% ...

As AI coding assistants become ubiquitous in enterprise development, a concerning statistic has emerged: 46% ...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

This new generation of botnets uses leaked API credentials or known exploits to enslave vulnerable and miscon...

Cybersecurity firm Cybersixgill has released a report on current trends in cybercrime. It shows that generati...
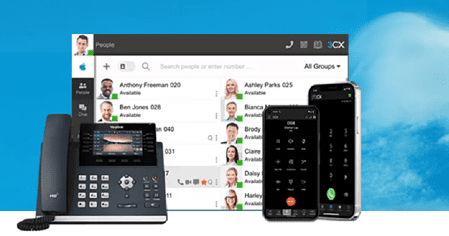
VoIP software vendor 3CX will soon implement a forced security upgrade of its progressive web application (PW...

Israeli cybersecurity company Sygnia has set its sights on RagnarLocker, a group of ransomware criminals. Usi...

Two new threat analyses expose a new player in the field of targeted hacking for intelligence gathering. N...

CrowdStrike announced this morning that it is expanding its CrowdStrike Falcon platform. The expansion includ...

Netskope is integrating its offerings with a new software service. Netskope Endpoint SD-WAN combines two tech...

Three-quarters of security vulnerabilities pose hardly any risk. The real danger comes from a very small numb...

Last week's security updates are now available for older iPhones, iPads, and Macs. This week Apple release...

Microsoft, Fortra and the non-profit organization Health-ISAC are jointly cracking down on providers of illeg...