
Securing agentic AI is still about getting the basics right
As agentic AI workflows spread across enterprises, security leaders face challenges in identity management, a...

As agentic AI workflows spread across enterprises, security leaders face challenges in identity management, a...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

Energy companies see cybersecurity as the biggest risk to their business. Two-thirds of energy professionals ...
A new variant of the infamous Mirai malware has been discovered. Murdoc_Botnet targets AVTech cameras and Hua...

Hewlett Packard Enterprise (HPE) is investigating claims of an intrusion after IntelBroker claimed to have st...

AI assistants make mistakes just like humans, and they may require extra care and attention. Prompt Security ...

Paris-based HarfangLab wants to differentiate itself from its endpoint security rivals. CSO Anouck Teiller ex...

Russian state hacker Star Blizzard is conducting a new spear-phishing campaign. The goal is to compromise Wha...

Microsoft has fixed a well-known problem. That caused Microsoft 365 apps and Classic Outlook to crash on Wind...

rsync, a veteran file synchronization tool, contains several vulnerabilities. The new 3.4.0 release is alread...
SentinelOne's security analyst can now be used with third-party data. This expansion should accelerate cybers...
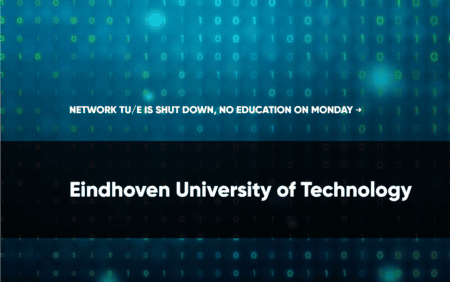
Eindhoven's Technical University (TU/e) is in the midst of recovering from a hack. Although the attack took p...