Everything there is to find on tag: Security.
Phishing campaign bypasses security corrupt Word documents
A new phishing attack abuses Microsoft Word's recovery option by sending corrupt Word documents as e-mail att...
Everything there is to find on tag: Security.
A new phishing attack abuses Microsoft Word's recovery option by sending corrupt Word documents as e-mail att...

GitHub has launched a new investment program worth 1.25 million dollars (1.85 million euros). This program sh...

F5 has opened its AI Gateway to a limited number of customers in early access. This containerized toolset is ...

Cisco reports a major security flaw in its Ultra-Reliable Wireless Backhaul systems. An unauthorized person i...


Data-centric AI development platform company Dataloop has dialled into Qualcomm with the aim of fuelling AI m...


Cognizant and Palo Alto Networks announce a strategic partnership to deliver AI-driven cybersecurity solution...
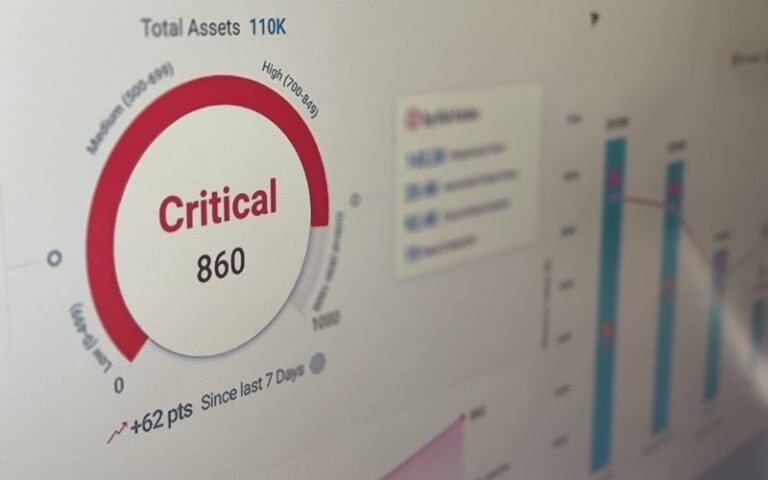
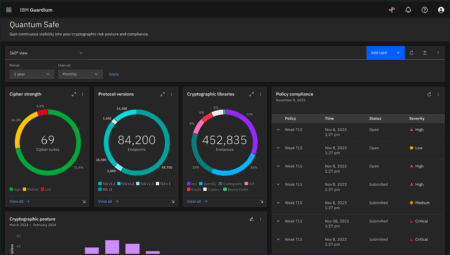
Cloud computing security and compliance specialist Qualys held the main Americas leg of its annual multiple-l...