Chances are you’ve never heard of Zscaler. Yet the company provides security services for many organizations worldwide, with 100 data centers and the largest security cloud in the world.
Zscaler was founded eleven years ago before anyone had heard of the cloud. Salesforce was one of the first cloud services to become popular, while the name ‘cloud’ was yet to be invented. At Zscaler, they foresaw that in the end, almost everything would go to the cloud, with security risks as a result. You simply can’t put a fence around the cloud like with your on-premise data center. A solution had to be found for this, which was Zscaler’s mission.
You simply can’t put a fence around the cloud
Today’s businesses migrate everything to the cloud, but they do very little in terms of security. They often depend wholly on the security of the cloud provider. The simplest solution could be to have all your cloud services routed through your own data center, because then you can put a firewall in between and in theory you have that ‘fence’. However, the fact is that we are becoming increasingly mobile, and organizations are operating more and more internationally. You don’t want to route your data traffic via Amsterdam when you are in the United States, or vice versa. That simply takes far too long, and faster response time is also important.
With a 100 data centers, you always have a fast connection.
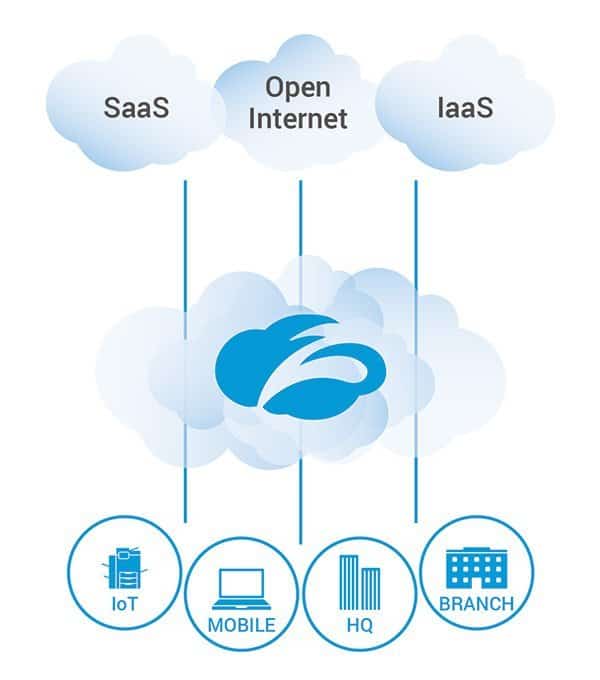
Zscaler offers this ‘fence’, as it were, plus a whole lot more. The company delivers from more than 100 data centers around the world. Zscaler opts for reliable, carrier-neutral data centers, such as Equinix. The advantage of 100 data centers is that you always have a high-speed connection to the data center and your cloud services. There is always a node nearby, and within these Zscaler nodes, there are connections with all known cloud service providers. By using Zscaler, all internet traffic is encrypted and subjected to a number of security measures. The most obvious is a proxy between the client’s web traffic and the cloud, but also applications such as a firewall, data loss prevention (DLP), bandwidth control, cloud sandbox and behavioral analysis of the data traffic.
Zscaler only works with its own technology
The company itself develops all technology for their solution, and wants to deliver a security cloud platform built from scratch. It is, therefore, not a combination of all kinds of different known security products from other suppliers. Even the Next Gen firewall and DLP products have been developed entirely in-house and are very suitable for enterprises.
How does ZPA work?
What Zscaler does, as it were, is set up an SSL tunnel between each client or router in the office. This means that the connection between the client or the office location and the Zscaler data center is always encrypted. You can choose between an application on the client or connecting an entire company network or maybe even a combination of both. This will depend on the type of company.
The big advantage of Zscaler in comparison with a VPN is that the SSL tunnels used by Zscaler stand alone. Many VPN gateways are very easy to recognize and trace and therefore easier to hack, with all consequences. Once a hacker has found out about the VPN, he will often be on the entire company network. An SSL tunnel is simply a routing of the connection and therefore invisible from the outside.
What Zscaler does, as it were, is set up an SSL tunnel between each client or router in the office. This means that the connection between the client or the office location and the Zscaler data center is always encrypted. You can choose between an application on the client or connecting a complete company network or maybe even a combination of both. This will depend on the type of company.
The big advantage of Zscaler over a VPN is that the SSL tunnels used by Zscaler stand alone. Many VPN gateways are very easy to recognize and trace and therefore easier to hack, with all accompanying consequences. Once a hacker has found out about the VPN, he will often be on the entire company network. An SSL tunnel is simply a routing of the connection and therefore invisible from the outside.
Zscaler has the largest security cloud in the world
Because Zscaler now has more than 100 data centers in operation, it also has an enormous amount of data traffic within which it can analyze malware patterns. Zscaler is able to detect attacks on a company or an outbreak of malware at a very early stage. They have also developed the cloud sandbox for this purpose. If they find something that may be undesirable, they can place it in the cloud sandbox and monitor it for a number of days to see what it does. Because they can analyze so much data traffic, they make extensive use of behavioral analysis to detect possible hackers, malware or DDoS attacks at an early stage. Therefore, this behavioral analysis is also a defensive tool against advanced threat protection (ATP).
Connecting to cloud services
If a user is connected to Zscaler Private Access (ZPA), the user has authenticated himself and is connected to the nearest Zscaler data center. Based on this authentication, Zscaler or the system administrator can determine which services you can or cannot connect to. Zscaler has connectors with many large cloud services so that a private connection can be established between Zscaler and the cloud service for the specific user. The connection between the cloud service and Zscaler is therefore not shared with the rest of the company, which is often the case with VPNs.
Zscaler cannot ‘see’ any data
Although Zscaler has various security mechanisms, they only look at patterns and metadata. For example, they can see that a Word document is sent with the name “financial results Q1.docx”, that the document was created on 10 June 2018, from which IP address it comes and to which IP address it goes. Zscaler cannot see the contents of the file. This has advantages and disadvantages.
The advantage is that it meets the privacy requirements of almost all enterprise organizations. The disadvantage is that Zscaler can only stop files that show suspicious behaviour immediately or within a few days. If malware is spread but is programmed to keep quiet for the first few weeks, it may not be detected as dangerous when it enters the network. However, due to its integration with detection mechanisms, Zscaler can block traffic that goes to suspicious sites afterwards. A good endpoint security solution is certainly recommended in combination with Zscaler.
If something is detected that is dangerous, or potentially dangerous, it is automatically detected by behavioral analysis. Action is automatically taken, either by quarantining the file or directly in the sandbox. It is also possible that the connection will simply be blocked. The company’s IT administrator or the person assigned to it can then decide what action to take. No people from Zscaler are involved, because people are, potentially, a weak link and the company does not want to risk that. Everything happens on the basis of AI.
Encryption important, but not at every company
Zscaler now protects some 60 million users in 185 countries with its services, a total of some 2,800 companies. The company offers SSL scanning, which is still a weakness for about half of the companies in Europe because they do not use SSL detection. Companies still use unsecured connections in almost 50 percent of cases.
That number is still much higher than you would expect. Certainly, due to the rise of SSL, things seemed to be going very well in recent years, but malware scans of encrypted traffic are still far from being carried out at all companies. The main reason for this is the possible costs. SSL-decryption for a malware-scan needs a lot more computing power, which means increased costs.

Speed gain
The use of Zscaler can also lead to considerable speed gains in some countries. If a company uses Office 365 and the Microsoft data center is 1000 kilometers away, then a Zscaler data center 100 kilometers away can generally achieve a faster connection. This is possible because Zscaler has direct connections with a huge number of cloud partners.
Insights into what employees do
If customers choose to share data traffic with Zscaler, it is also possible to use analytics. For example, which websites are visited (and how often), and what the security features have run into in the data traffic. That way, for example, it can be discovered that a salesperson in the office spends 40 percent of his/her time on YouTube, 35 percent on Facebook and only 25 percent on things like e-mail and a CRM solution. Based on these analytics, you can see that the employee can significantly improve their work and that it might be time for a stern conversation.
Privacy
Of course, privacy is also important. That is why the company itself determines which data traffic it shares with Zscaler and which analytics will be released, even if a user travels around the world and is in Los Angeles, for example. The user will then log in to the Zscaler data center in Los Angeles. As soon as this happens, the profile will be loaded from the data center in the country of origin, e.g. Amsterdam. This profile will be used to verify the details. The data traffic logs are temporarily stored in memory, not on disk. This only happens in the country of origin.
According to Zscaler, VPN is going to be the loser in the long term, and companies are more likely to opt for the Zscaler solution or something competitive. Security is important, and problems can be prevented by managing and analyzing the entire chain.
