
Identity has become malleable for cyber attackers
Although cyber attackers prefer to target unprepared victims, they have the means to strike even maturely def...

Although cyber attackers prefer to target unprepared victims, they have the means to strike even maturely def...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

Meta has experienced an internal security incident in which an AI agent played a role in temporarily exposing...

Cohesity has integrated 'next-generation' malware scanning powered by Sophos directly into Cohesity Data Clou...

Rubrik has launched Data Protection for Google Workspace. The release adds air-gapped backups and rapid recov...

Nile has announced new security features for its Secure Network-as-a-Service platform. At its core is a zero-...

The U.S. government is warning companies to better secure their Microsoft Intune management environments foll...

Although cyber attackers prefer to target unprepared victims, they have the means to strike even maturely def...

SpecterOps adds support for Okta, GitHub, and Mac environments to BloodHound Enterprise. With OpenGraph exten...
The Linux Foundation has announced that it is receiving a total of $12.5 million in grants from a group of te...

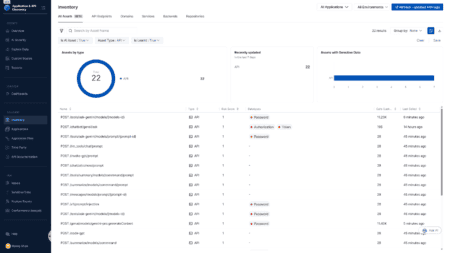
1Password is introducing Unified Access Pro, a platform that manages credentials and access for people, AI ag...
Harness is expanding its DevSecOps platform with AI Security and Secure AI Coding. The first module detects, ...