DevOps automation company Puppet announced on Wednesday the introduction of new integrations, during its Puppetize Digital 2021 virtual conference. The aim is to support more automation via self-service at a large scale and secure hybrid infrastructure better.
The announcements at the conference included Compliance Enforcement Modules combined into Puppet Comply, an integration for ServiceNow Graph Connector Program for Puppet Enterprise, and a new malware scanning capability for publications on Forge.
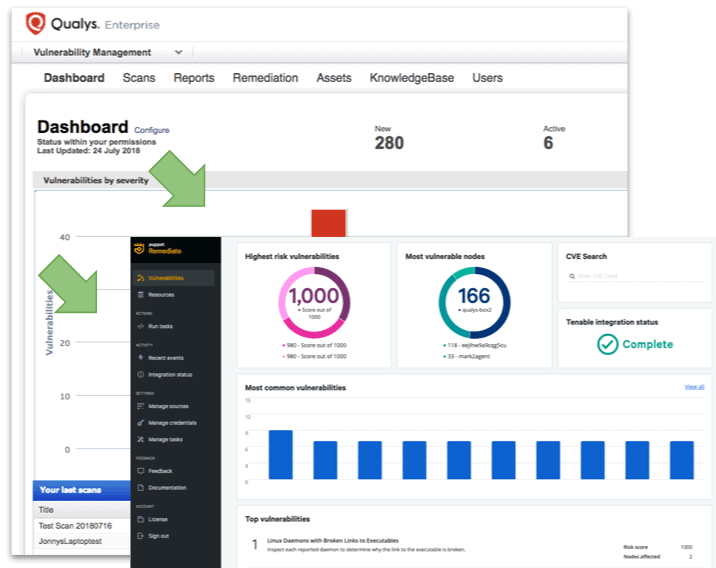
Puppet has taken note of the flood of vulnerabilities announced each day and started focusing on infrastructure security compliance across environments for better decision-making.
Making compliance easy
Creating a culture of increased collaboration between teams needs enhanced visibility and automation for DevOps teams in hybrid, cloud, and native environments. The Compliance Enforcement Modules for Puppet Comply will provide customers with compliance remediation and enforcement policies that work with Puppet Enterprise.
The modules allow the enforcement of policy-as-code configuration management that conforms with the Center for Internet Security Benchmarks for both Linux and Windows.
It delivers the baseline of cybersecurity’s best practices for code configurations, according to industry standards regarding security compliance.
ServiceNow Graph Connector and malware scanner in Forge
ServiceNow customers can take in relevant and accurate data from Puppet-managed assets into their configuration management database for informed decision-making about hybrid cloud infrastructures.
It does this by automating data collection and reporting for all ServiceNow products.
In addition to that, a new malware scanner that should be operational by the end of the year is available on Forge, Puppet’s module marketplace, to check newly published modules for flaws. The feature should reduce the number of modules that reach implementation stages while containing vulnerabilities.
This rollout will focus on Supported modules, then move to Partner and Approved modules.