Samsung and Microsoft have announced that they will dramatically strengthen the security level of Galaxy smartphones. The Korean giant describes the innovation as the world’s first “on-device attestation” for phones, extending the sharpest security standards to smartphones.
In the press release, Samsung outlines the benefits of hardware-based attestation. Microsoft also describes the extensive possibilities of this security set-up. For example, a company can now remotely measure the device’s identity and health to ensure it has not been compromised from within Microsoft Intune. It builds on existing Samsung Knox capabilities and hooks into the existing Windows application. The rationale for this deepening of security isn’t hard to fathom: many organizations are accepting of a Bring Your Own Device (BYOD) culture, which allows otherwise unauthenticated hardware to connect to corporate networks if no further security steps are taken. According to Samsung, the new capabilities can provide more flexibility regarding security approaches.
Zero trust and integrated
Samsung pojnts out that its Knox security has been on the market for 10 years and has been activated on more than a billion Galaxy phones. The move to partner with Microsoft is primarily to bring endpoint management together as much as possible, integrating these billion+ devices. This is certainly relevant for organizations, as decentralized management of IT drives inconsistencies when it comes to security. Instead, layered protection against cyber threats requires a unified policy that relies as much as possible on zero-trust. This is especially important in sectors where security requirements from the government are substantial, such as banks, the healthcare sector and heavy industry. These parties can often be targeted by cybercrime, as was recently the case with LockBit 3.0.
Read also: LockBit shuts down seaport in Japan: OT attacks have a huge impact
Within Microsoft Intune
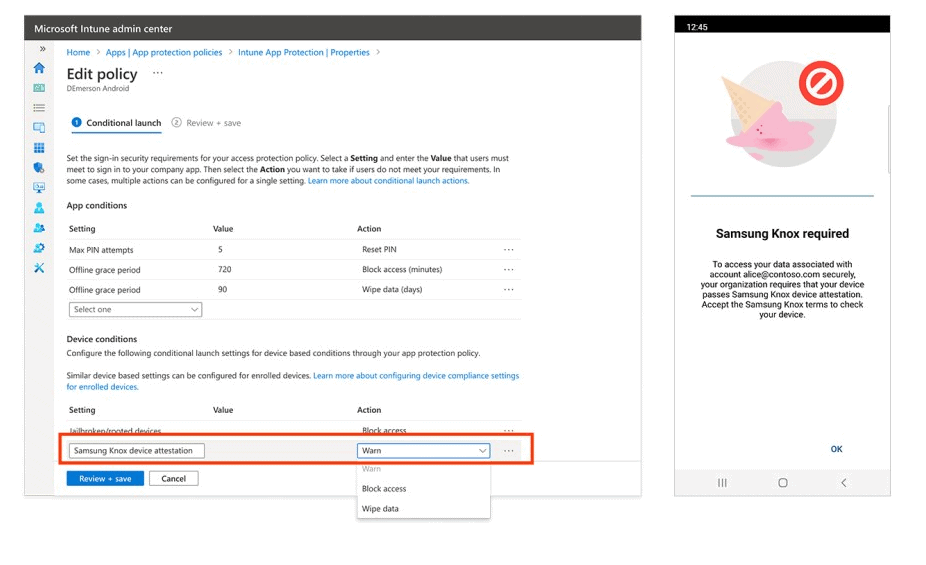
Users can now easily set a policy within Microsoft Intune for Samsung phones. In a drop-down menu, the behaviour can be determined in case of any problems that crop up with this hardware. Because device attestation occurs on the smartphone itself, it does not require traditional network connectivity and server infrastructure to verify the device.
