Security company Trellix warns of a sharp increase in advanced phishing attacks on Facebook users. In the second half of 2025, researchers saw a rise in the use of the ‘Browser-in-the-Browser’ technique, in which attackers simulate fake login windows that are almost indistinguishable from the real thing.
With more than 3 billion active users, Facebook remains an attractive target for cybercriminals. In recent months, however, the approach has been evolving rapidly. Whereas phishing used to revolve mainly around simple fake links, attackers are now focusing on more technically complex methods.
The Browser-in-the-Browser (BitB) technique displays a fully simulated Facebook login window within the user’s browser. The fake window even contains the real Facebook URL in the address bar, making it virtually impossible to visually distinguish it is from legitimate login page. Criminals build these interfaces entirely from scratch, including hardcoded URLs designed to inspire trust.
Phishing via trusted platforms
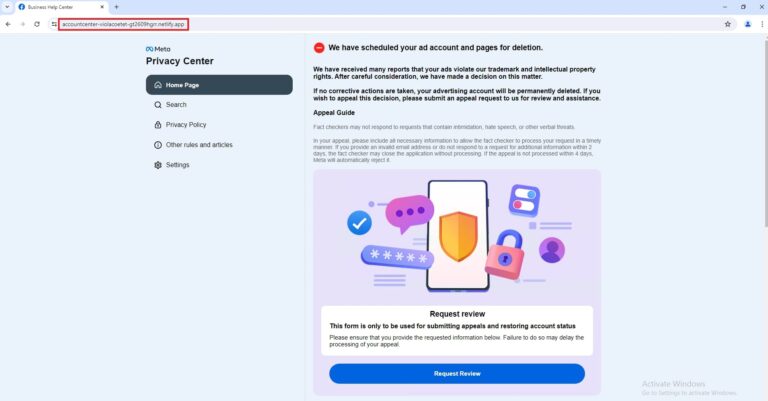
In addition to the BitB method, researchers are also seeing an increase in the abuse of legitimate cloud platforms. Attackers host their fake login pages on services such as Netlify and Vercel. This choice is understandable. Security filters trust these platforms, making it easier for phishing attempts to slip through the controls.
A typical attack starts with an email that pretends to be from a law firm. The email contains a shortened URL that redirects to a fake Meta captcha page via services such as lnk.ink. Once there, users are presented with a “Facebook login prompt” that steals their credentials.
The most common variants focus on account issues. Victims receive messages about alleged copyright violations, suspicious login attempts from unknown devices, or urgent security updates that require “immediate verification.”
What users can do
Trellix emphasizes that two-factor authentication (2FA) remains the most important defense. Even if criminals steal login credentials via a BitB attack, 2FA prevents them from actually accessing the account.
In addition, the company recommends not clicking links in emails about account issues. Instead, users should manually type facebook.com or use the official app to check their account status. Checking the full URL in the address bar also remains crucial, especially for references to netlify.app, vercel.app, or URL shorteners.