NetApp announces the availability of Spot Security. According to the organization, the solution is capable of analyzing and securing cloud, infrastructure and application data, network traffic and user behavior with AI identification of anomalies, threat prioritization and remediation support.
Spot Security appears under the umbrella of NetApp Spot, a solution for the efficient provisioning of infrastructure when deploying and managing VM and Kubernetes applications in Google Cloud, Azure or AWS.
NetApp Spot primarily serves to optimize the cloud resource consumption of applications. Accurate insight into the infrastructure required for applications is a secondary benefit, allowing the choice of cloud licenses that are actually cost-effective — and not just described as such. In this light, NetApp Spot assumes the role of a neutral watchdog.
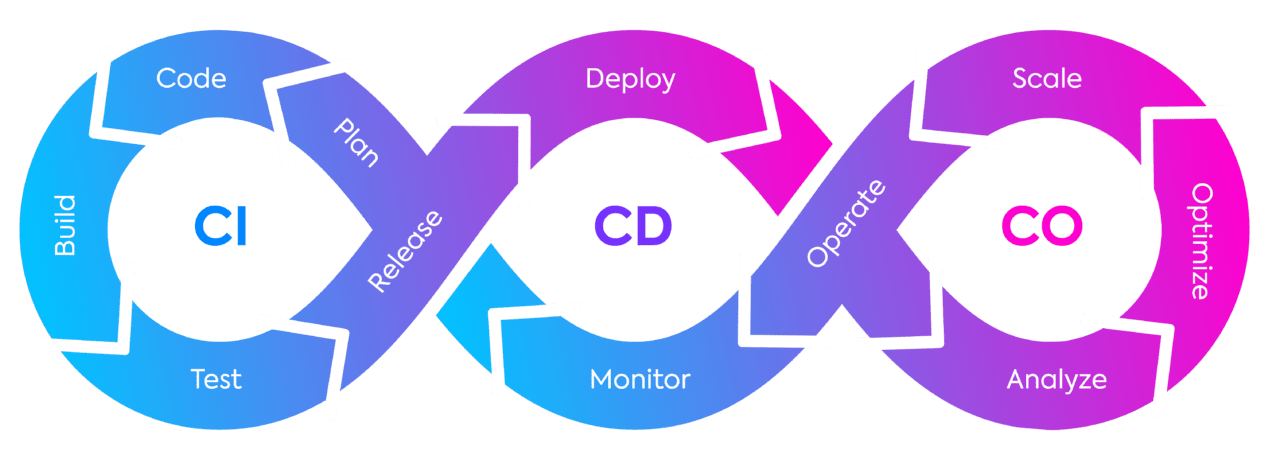
Thus, NetApp Spot is not a solution for the development or deployment (CI/CD) of VM and Kubernetes applications, but a complement to the CI/CD process, with a focus on cost-effective use of cloud resources.
The diagram below clarifies the latter. NetApp Spot provides Continuous Optimization (CO) and makes an entry after Continuous Deployment (CD), a process facilitated by various software, including but not limited to AWS CodePipeline and GitLab.
From Spot to Spot Security
Back to the news. The newly-launched NetApp Spot Security uses technology similar to the foundation with which NetApp Spot provides insight into the total usage of infrastructure and applications. Whereas NetApp Spot uses said insight to optimize application usage of infrastructure, NetApp Spot Security scans the data to flag anomalies and rank them by risk factor.
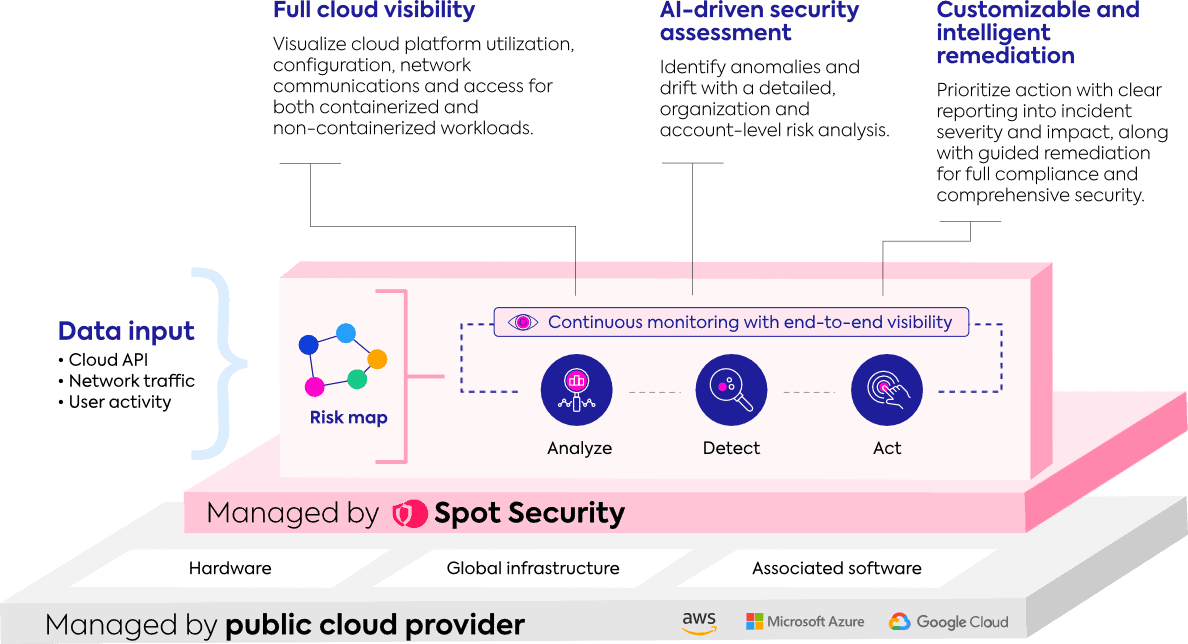
The solution does not automatically resolve threats. Instead, it advises on the actions required and supports where possible. Furthermore, NetApp Spot Security feeds from a broader data set than NetApp Spot, including data from applications and infrastructure, network traffic and user behaviour, as illustrated in the diagram below. A preview of the solution has been available through registration since October 20.