Security specialist JFrog warns of a bug in Apache Cassandra’s Nashorn engine that allows remote code execution in affected systems.
Apache Cassandra is an open-source distributed NoSQL database management system for handling large amounts of data on standard servers. The system, originally developed by Meta, provides high data availability.
This makes the tool particularly suitable for applications that monitor and analyze activity in large amounts of data, such as social media analytics and messaging platforms. Major users include Netflix, Reddit, Constant Contact and Cisco.
The threat
The vulnerability (CVE-2021-44521) has a score of 8.4. According to JFrog’s security experts, the vulnerability allows remote execution of malicious code (RCE).
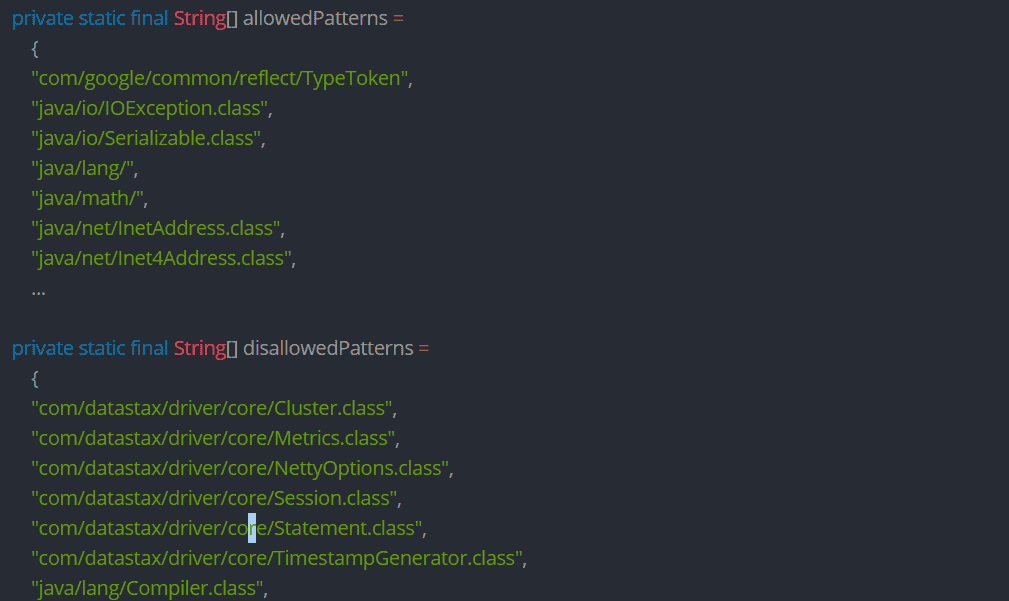
The problem occurs in the Nashorn engine within the Runtime environment of Apache Cassandra. Security specialists indicate that the Nashorn engine does not handle unverified code securely. Any organization applying Nashorn to unverified code is advised to move Nashorn to a sandbox environment. JFrog’s researches note that only non-standard Nashorn configurations are susceptible to RCE.
Patches
Apache has since released a patch. Users of Apache Cassandra are urged to update as soon as possible. The patch is integrated in v3.0.26 (for v3.0x), v3.11.12 (for v3.11.x) and v4.0.2 (for v4.0.x).