The cybercriminals behind the LastPass hack in August had access to the company’s systems for four days.
LastPass comes up with the conclusion after research in collaboration with Mandiant. The hackers managed to gain access to the systems by compromising an endpoint of a LastPass employee. This gave them access to the development environment. They were able to stay in the environment longer by posing as the hacked developer. This was possible after he successfully authenticated himself using multi-factor authentication.
No data captured
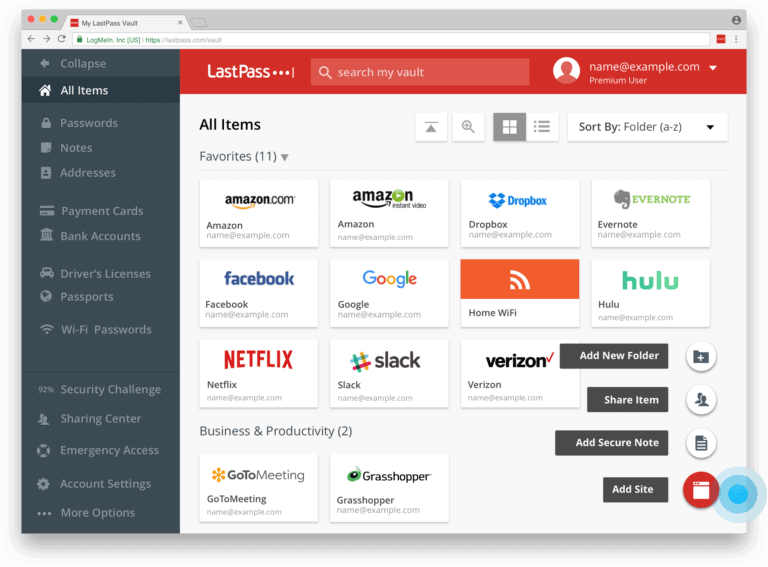
No important data was captured during the presence of the hackers, the researchers claim. The security systems prevented that, despite the access. The hackers did not gain access to customer data or customers’ encrypted password vaults in this way.
Also after examining LastPass’ source code and various builds, it was found that the hackers did not inject any malicious code. Again, the production stages of the code prevented this, LastPass said.
More security functionality
To prevent hacks in the future, LastPass has rolled out more extensive security and monitoring functionality for all endpoints within the organization. Additional threat intelligence capabilities and enhanced detection and prevention technology have also been rolled out for development and production environments.
Also read: Popular password manager LastPass hit by cyberattack