Rubrik SAGE: using AI to govern agentic workforces
As agentic AI systems move from proof-of-concept to production, enterprises face a security challenge: how do...

As agentic AI systems move from proof-of-concept to production, enterprises face a security challenge: how do...
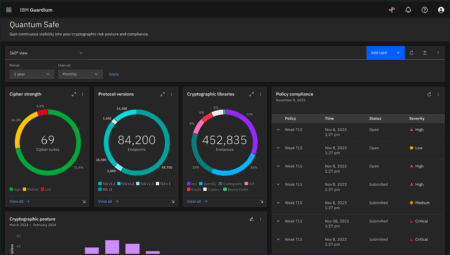
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

Apple will encourage and reward ethical hackers for finding bugs in its Private Cloud Compute (PCC) system fo...


Cegeka expands its Identity & Access Management (IAM) portfolio through a partnership with Belgian firm E...

A newly discovered vulnerability in FortiManager from networking and security specialist Fortinet has been ac...

U.S. cybersecurity watchdog CISA recently issued a consultation list of new mandatory security requirements. ...

The App Store and Google Play Store offer a treasure trove of applications. Those themselves regularly presen...