The widely used WordPress plugin Elementor Pro can be abused to take over websites.
According to a NinTechNet researcher, Elementor Pro has a vulnerability that allows cybercriminals to take over millions of websites. The vulnerability affects the plugin’s access control.
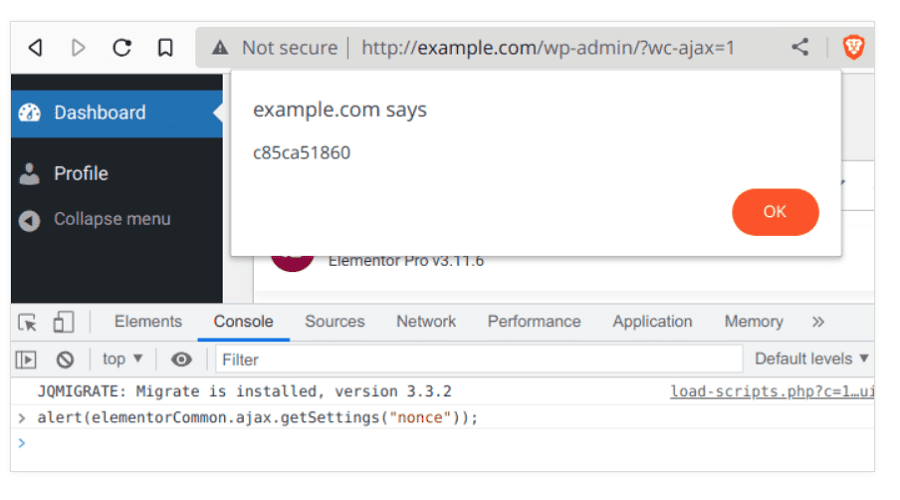
At issue is a component in the plugin’s built-in editor for websites using WooCommerce. The component allows the modification of WordPress options in the underlying e-commerce database. However, access to this is not validated, leaving it open to anyone logged in, not just specific users.
Cybercriminals can therefore take over admin privileges for an affected website. They can then create an admin account, enable registration, set the default role to “administrator,” change the administrator’s email address and, by changing the site url, redirect traffic to external malicious websites.
Active exploits and indicators
From research by security firm PatchStack, the exploit now appears to be actively deployed. Companies using premium version of Elementer Pro are advised to upgrade to version 3.11.7 and higher. Earlier versions are all vulnerable. Users would also do well to watch for “infection indicators. The indicators are:
- Traffic from the IP addresses: 193.169.194.63, 193.169.195.64 and 194.135.30.6.
- Uploads of malicious files: wp-resortpack.zip, wp-rate.php and lll.zip
- Site URLs changed to: away[dot]trackersline[dot]com
Also read: WordPress to force-install a security update to thousands of websites