Microsoft researchers have discovered fifteen vulnerabilities in the CODESYS V3 software development kit. After several steps, it is possible for malicious actors to carry out a denial-of-service attack, even if it is difficult to accomplish.
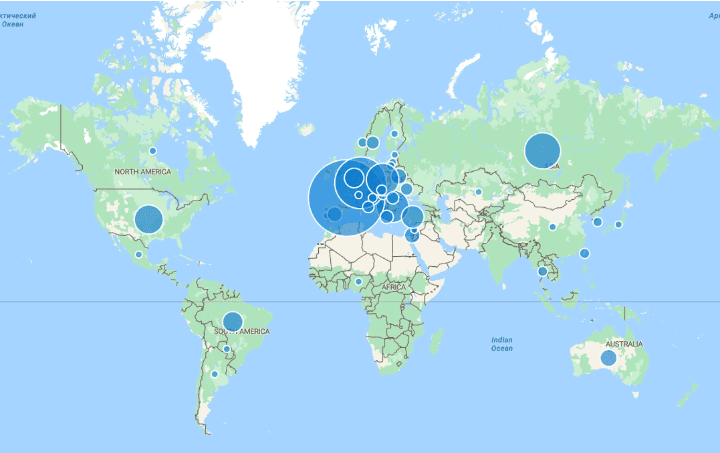
The CODESYS tool handles industrial automation and is used by many major players to control equipment. For example, it is used by industrial players such as Schneider Electric, Eaton Corporation and WAGO. In total, the tool is compatible with about 1,000 different types of equipment from more than 500 manufacturers, as Microsoft points out.
Tags as danger
The research team discovered 15 vulnerabilities, all of which they describe as “very serious.” They studied a two PLCs (Programmable Logic Controllers) where they were able to figure out the CODESYS V3 protocol. The so-called tag decoding mechanism was the culprit. Components within CODESYS use tags, which can represent all kinds of data types. However, there was no mechanism in limiting the format of a tag once a component adopted it. This led to a buffer overflow, after which attackers could take over a device completely. This may include the systems that control a power plant’s inner workings, or a variety of other deployments.
In short, you need quite a bit of expertise when it comes to CODESYS. That already requires penetrating a relevant business environment. Patches have also been around for a while: CODESYS had started working on them in March after obtaining information about the vulnerabilities from Microsoft in September 2022. Still, for both OT and IT, patch management is far from being adhered to. Therefore, this exploitation remains dangerous, so for CODESYS users it is important to check whether everything has been updated.
Also read: Vulnerabilities in critical infrastructure could have massive consequences