Recent research by IBM Security X-Force finds that Europe faced the most cyber attacks in 2023. High cloud adoption that increases the attack surface is the main reason.
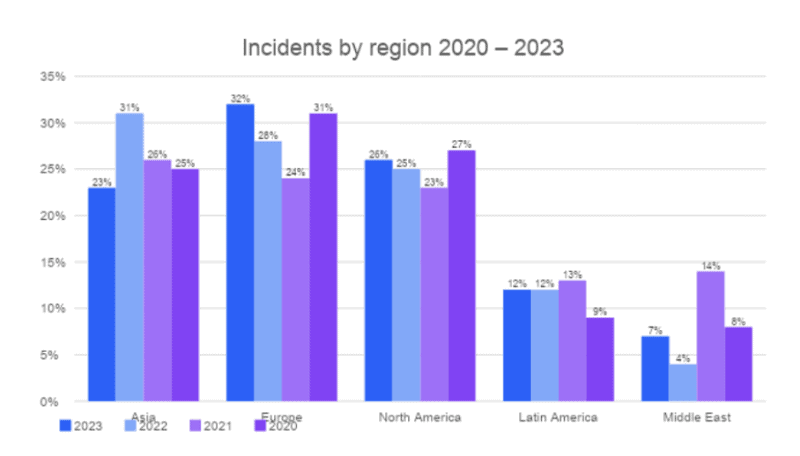
The annual IBM X-Force Threat Intelligence Index 2024 shows that Europe suffered the most cyber attacks of any world region in the past year. Of all cyber attacks in 2023, 32 percent targeted this region, up from 24 percent a year earlier.
Reasons
According to researchers from IBM, there is a reason that Europe was so in demand by cybercriminals last year. The number of ransomware attacks in the region was primarily significant (26 percent of the total). The high number of attacks occur because European companies are using cloud environments en masse. This increases the attack surface for cybercriminals. Especially when hackers already have access to valid login credentials for cloud accounts.
Within Europe, the most attacked countries were the United Kingdom, with 27 percent of total attacks. This was followed by Germany with 15 percent and Denmark with 14 percent. Portugal took fourth place with 11 percent. Large countries such as France and Italy each scored 8 percent of the total number of attacks.
Legitimate login credentials main ‘entry point’
Another key finding of the researchers is that cybercriminals are increasingly interested in stealing in-use login credentials to use legitimate user identities. The misuse of legitimate login credentials increased 71 percent in 2023. This made misuse of legitimate login credentials the most common “entry point” for attacks on victims’ environments in the past year.
Further key conclusions of the researchers included that the number of attacks that led to data theft or leaks increased by 32 percent. The specialist concluded that attackers today prefer to steal and sell data rather than encrypt it for extortion.
Finally, the security specialists noted that in the past year, most cyber attacks took place on so-called critical infrastructure. They were said to account for 70 percent of the total. More than 85 percent of these types of attacks were possible through public applications, phishing emails and the use of legitimate login credentials.
Also read: Ransomware payments reach record high: more than 1 billion euros
