Credentials of 15 billion accounts are being sold on the dark web, according to research by Digital Shadows. The price ranges from under ten euros for access to streaming websites to about 100.000 euros for access to large companies.
The research ‘From Exposure to Takeover: The 15 billion stolen credentials allowing account takeover‘ was the result of an eighteen-month study by security researchers from Digital Shadows. The team eventually found 15 billion credentials that had been obtained through 100.000 data breaches, of which 5 billion were unique.
The research also revealed that the number of stolen usernames and passwords in circulation has increased by 300 percent since the last research was conducted in 2018. The log-in data of customers turned out to be the most common with an average selling price of 13.62 euros. Credentials for financial institutions such as banks were the most valuable with an average selling price of 62.59 euros. Of all the advertisements on the dark web, 25 percent belongs to this category.
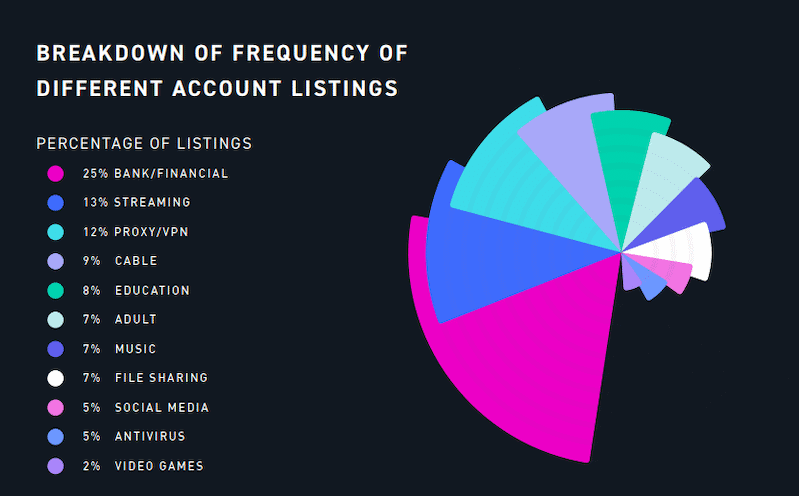
Access to antivirus programs also proved popular with an average price of 19.13 euros, but access to media streaming sites, social media, file sharing, and VPNs was sold for less than ten euros.
Access to large companies
Credentials for essential business systems of large (and smaller) companies are also traded on the dark web, but prices are much higher. These credentials are sold at an auction to the highest bidder and researchers at Digital Shadows came across figures ranging from 441 euros to 106.000 euros with an average of 2770 euros.
A new noteworthy development is that of the ‘account takeover-as-a-service’ where criminals can rent the login details of an account for a certain period of time, often for less than 10 euros.
Digital Shadows finds the number of available login details shocking. “Some of these exposed accounts can (or do have access to) incredibly sensitive information. Details uncovered by one breach can be re-used to compromise accounts used elsewhere.”
Tip: Why cybercriminals use forums and the dark web on a large scale
