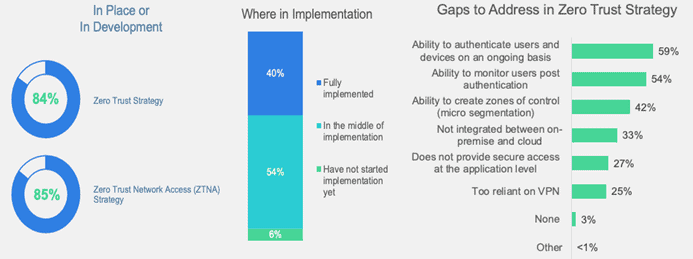
Most companies consider implementing a zero trust policy, but struggle with its actual implementation.
In a survey by Fortinet, over half of the companies indicate difficulties translating a zero trust vision into practical measures and solutions. Especially the lack of consistent authentication of users and devices is seen as a considerable problem. Similarly, many respondents note difficulties monitoring users after they have been authenticated.
Fortinet finds the gaps to be worrying. The problems indicated are the core components of a zero trust policy. Therefore, the researchers state, the actual contents of zero trust policies among the surveyed companies is anyone’s guess. Terms like ‘zero trust access’ and ‘zero-trust network access’ are used interchangeably.
Difference in priority
In addition, company priorities can vary quite a bit. The survey shows that the highest priority for zero trust is minimizing the impact of security incidents, followed by securing remote access and ensuring business continuity. Other priorities are improving the user experience and gaining more flexibility to provide security anywhere. Companies find the main benefit of zero trust to be integrated protection of a company’s digital attack surface.
Requirements and difficulties
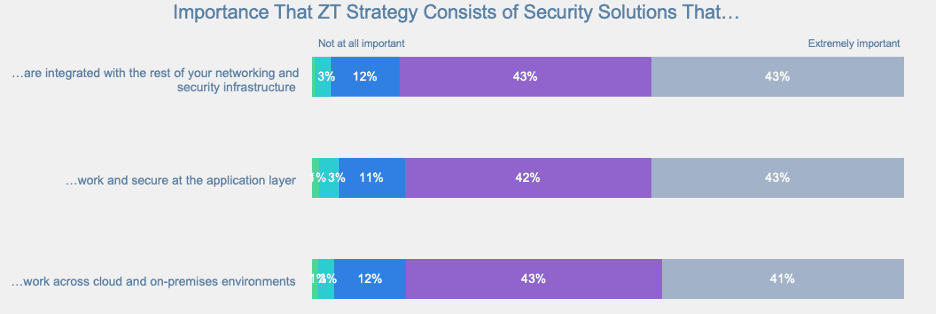
In addition to priorities and benefits, most respondents indicated that zero-trust solutions must integrate well with existing infrastructure, work processes in cloud environments and in on-premises environments. Most respondents find it very difficult to comply with the condition in their extended networks. This is partly due to a lack of specialized personnel. Therefore, a small portion opts for different strategies when implementing zero trust policies and environments.
Fortinet’s response
Fortinet indicates that companies can overcome the difficulty of implementing a zero trust policy. This includes using an integrated security platform that applies all the basics of zero trust to the entire IT infrastructure, including all endpoints, cloud and on-premises environments.
Tip: Fortinet guarantees secure network access with Zero Trust