Security researchers have found 23 major vulnerabilities in BIOS/UEFI software. The software is present in systems from major vendors such as Intel, Microsoft, Lenovo, Dell, Fujitsu, HP, HPE and Siemens.
Binarly found the vulnerabilities after the discovery of MoonBounce, a new malware family. The malware can embed itself in the BIOS chip of computing systems and deploy malware from there.
23 new vulnerabilities
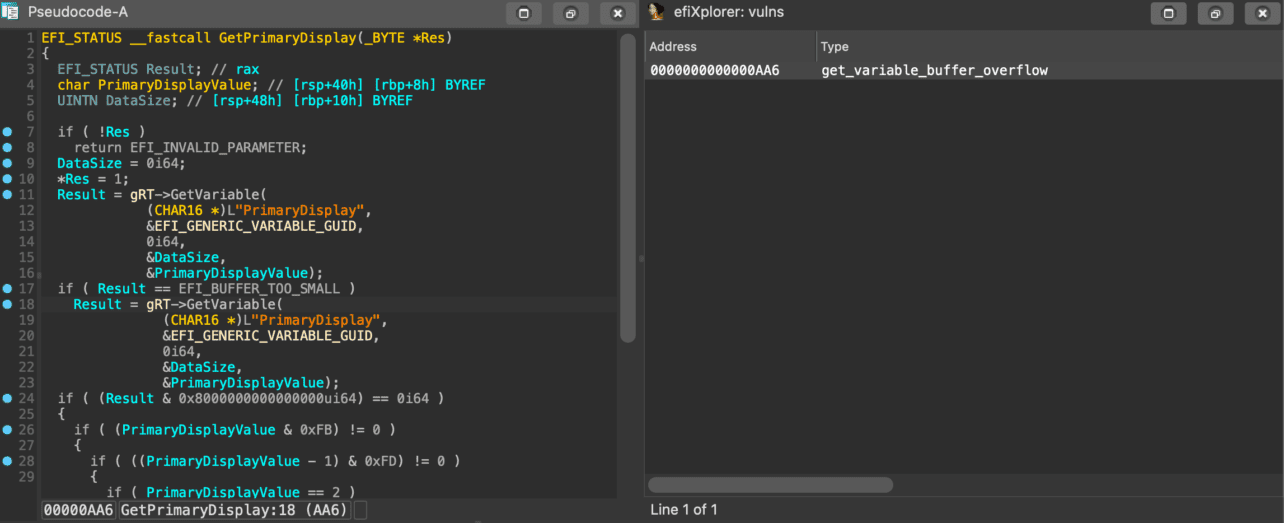
The researchers encountered 23 new vulnerabilities in BIOS/UEFI software. Some — if not all — of the vulnerabilities remain present. Security mechanisms can be bypassed regardless of formatting and reinstalling. That’s particularly problematic for the UEFI vulnerabilities: they serve as a springboard for installing additional malware and infected firmware images.
The vulnerabilities found in UEFI software can be used to bypass security features such as Secure Boot, Virtualization-Based Security and Trusted Platform Modules.
The vulnerabilities primarily occur in systems using InsydeH20 software. This is a firmware framework for rebuilding motherboard BIOSs/UEFIs. Some systems from the vendors mentioned above feature Insyde’s firmware SDK for building motherboards.
Multiple systems affected
Initially, Binarly researchers found the vulnerabilities on systems from Fujitsu. Further investigation revealed that the vulnerabilities were present on the systems of Intel, Microsoft, Lenovo, Dell, Fujitsu, HP, HPE, Siemens and Bull Atos, among others.
At this time, the vulnerabilities have been reported to CERT/CC’s Vulnerability Notes Database. Binarly developed a tool that allows companies to check their systems for vulnerable code patterns. Official fixes are expected in firmware updates later this year.