Chinese state hackers launched a Tarrask malware attack on Windows. The method circumvents Windows Security via the Windows Task Scheduler.
The state hackers are known as Hafnium. Microsoft warns that Hafnium has targeted Windows and is actively deploying Tarrask malware. The malware is designed to avoid Windows Task Scheduler’s integrated security and hide from basic monitoring.
Hafnium has been on the radar for some time. Last year, the hackers carried out a major attack on Microsoft Exchange.
Bug in Windows Task Scheduler
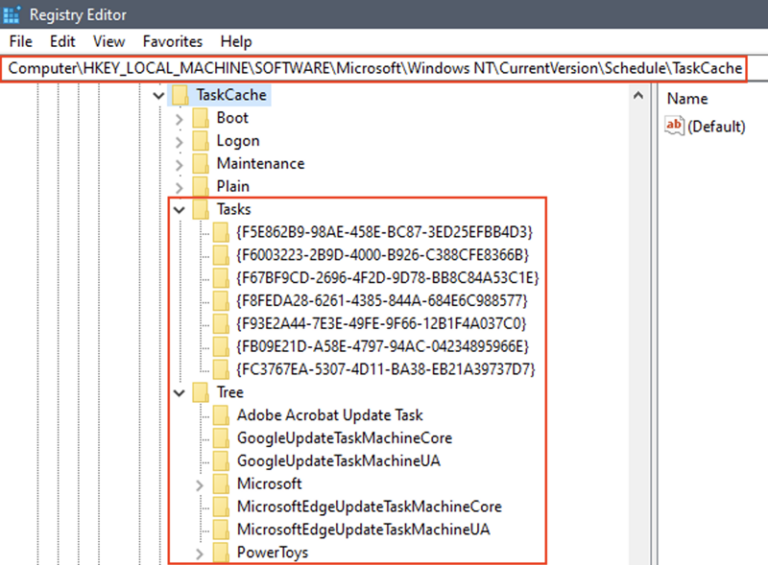
The hackers exploit a bug in Windows Task Scheduler to clean their tracks. Furthermore, Hafnium removes a Security Descriptor registry value to wipe all traces from on-disk malware. These measures allow Hafnium to operate covertly. Microsoft says that the hackers typically pop up sometime after infection to run various commands.
Mitigation
Microsoft is working on a fix. The tech giant urges organizations using Windows to manually check the Windows Registry for tasks executed without a SD value (security descriptor) in their Task Key.
Furthermore, the Security.evtx and Microsoft Windows TaskScheduler/Operational.evtx logs can reveal hidden Tarrask processes.
Finally, network connections can be logged by toggling ‘TaskOperational’ in the Microsoft Windows TaskScheduler/Operational Task Scheduler.
Tip: Microsoft Exchange Server hacked, what are the consequences?
