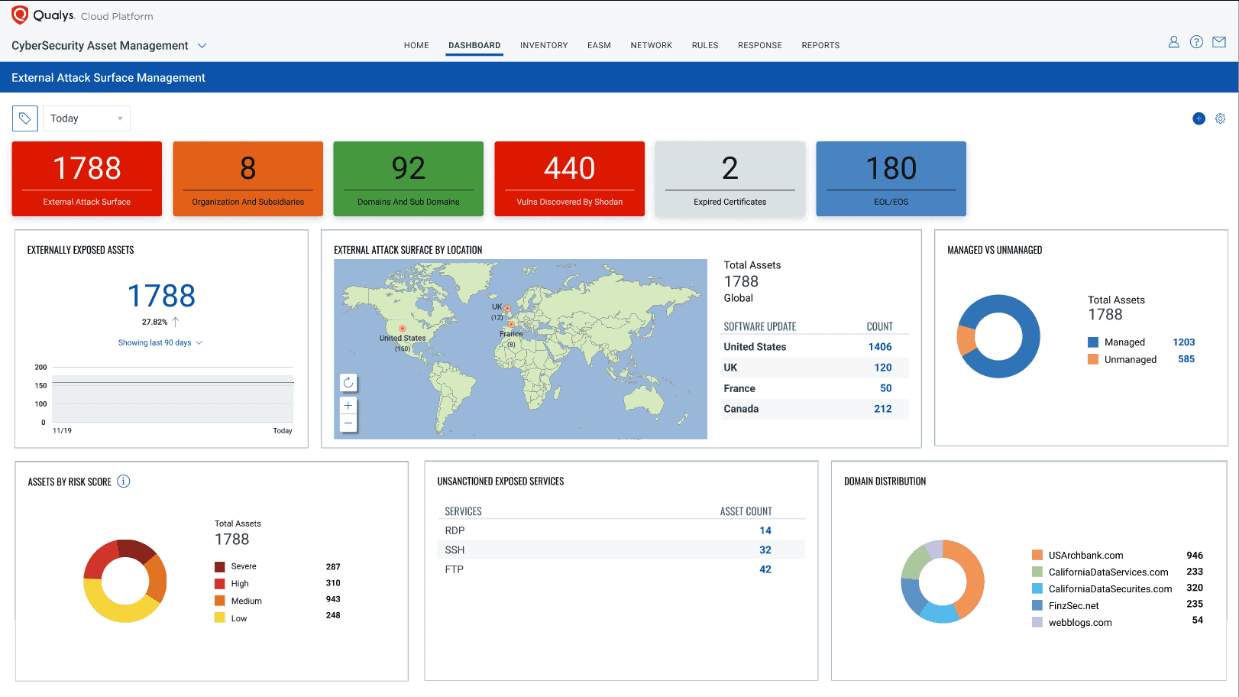
Qualys added external attack surface management (EASM) capabilities to CyberSecurity Asset Management 2.0, a solution that detects unknown systems in infrastructures. The new capabilities allow users to view an infrastructure from the perspective of a hacker. Each internet-facing asset is presented in a central overview.
It’s virtually impossible to secure an invisible device or program. Oversight is necessary for cybersecurity. Asset management solutions map the hardware and software of an infrastructure.
Qualys CyberSecurity Asset Management (CSAM) helps companies find unknown devices and outdated software. The solution has been generally available since 2021. Qualys scheduled the first major update (2.0) for mid-September 2022.
Although the deadline approaches, new features are still underway. Qualys recently announced that the release includes external attack surface management (EASM) capabilities. The capabilities provide an understandable overview of internet-facing assets.
Internet-facing assets are accessible from the outside. Any unknown system poses a problem, but unknown systems that connect to the internet are particularly risky. CSAM already makes it possible to take inventory of internal systems. Version 2.0 extends the overview of Internet-facing assets.
Integration with Qualys VMDR
The service doesn’t resolve vulnerabilities on its own. Users are alerted to weak spots, but will have to reinforce security on their own. The latter can be automated with Qualys Vulnerability Management, Detection and Response (VMDR). The solution integrates with CyberSecurity Asset Management and makes it possible to automate security workflows such as patch management.
Both solutions run on the Qualys Cloud Platform. Licenses are sold separately. The new external attack surface management capabilities are currently available in the preview of Qualys CyberSecurity Asset Management 2.0, a beta for existing customers. General availability will follow in mid-September 2022.
Tip: Dutch startup Hadrian receives €10 million for pentesting
