CyberArk launches Secure Browser for secure access
With the CyberArk Secure Browser, companies can build additional security and privacy safeguards into employee browser sessions.
CyberArk has experience in privileged access management. This allows employees' and partners' access rights to applications to be controlled so that only authorized us... Read more

CyberArk releases online ransomware decryptor
CyberArk recently released an online version of its open-source White Phoenix ransomware decryptor. With it, the company aims to help ransomware victims get their files back.
CyberArk's White Phoenix ransomware decryptor was already available as a Python project on GitHub, but the security compa... Read more

CyberArk Secrets Hub streamlines AWS secret management
Security provider CyberArk unveiled a new security solution for AWS and several improvements to its current product line.
The new solution, CyberArk Secrets Hub, allows developers to access AWS secrets with a straightforward method using AWS Secrets Manager. Using existing procedures and infrast... Read more

‘Vulnerability in Windows RDP protocol enables MITM attack’
A vulnerability in the Windows Remote Desktop Protocol (RDP) allows users connected to a remote machine to access connected devices of other users. The threat was recently observed by security specialists at CyberArk Labs. Hackers can exploit the vulnerability for a Man-In-The-Middle (MITM) attack.... Read more

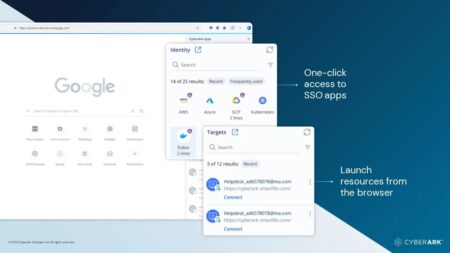
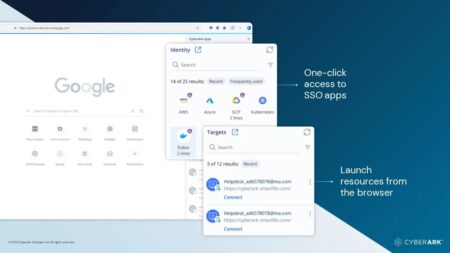
CyberArk expands Identity Security Platform with new services
During CyberArk Impact Live, CyberArk announced new enhancements to its Identity Security Platform. With this privileged access management platform, CyberArk aims to provide its customers with a holistic approach to providing secure access to users anywhere, anytime, regardless of the device they a... Read more

CyberArk: be careful with the security of privileged accounts
Security firm CyberArk has conducted a study on the protection of privileged accounts. Such accounts have increased access to corporate networks and are therefore very important to control.
According to CyberArk, privileged accounts play an important role in almost all major data leaks. Especial... Read more
 Expert talks
Expert talks

What is privileged access management?
Privileged access refers to all accounts with more access rights than a default user. It can be either human or non-human users such as applications and machine identities. Privileged access enables organizations to secure their infrastructure and applications, conduct business more efficiently, an... Read more

CyberArk launches tool for identifying Shadow Admin accounts
CyberArk, a cybersecurity company, launched an open-source tool to identify shadow Admin accounts in AWS (Amazon Web Services) and Microsoft Azure clouds. The tool will help organizations that use the cloud, detect and prevent Shadow Admins through targeting and securing the legitimate Admins in AW... Read more

CyberArk Alero enhances Remote User Security with new Authentication
CyberArk, a leading global firm in providing privileged access management services, today unveiled new features for CyberArk Alero that allows remote customers to securely access CyberArk’s managed critical services from any mobile equipment- including non-smartphones.
“There are nearly 1.3... Read more

Working from home poses great risk to company data and systems
Working from home has a significant impact on the risks to which company systems and sensitive data are exposed. Other family members often use company equipment, and passwords are also used for various applications.
CyberArk conducted a survey among 3000 remote workers from various European cou... Read more