Everything there is to find on tag: malware.

Microsoft discovers backdoor that exploits OpenAI API
Microsoft researchers discovered a backdoor that exploits the OpenAI Assistants API for command-and-control c...
Everything there is to find on tag: malware.

Microsoft researchers discovered a backdoor that exploits the OpenAI Assistants API for command-and-control c...

The Chinese cyber threat UNC6384 was already known to target diplomats in Southeast Asia. Now it appears that...

The Russian cyber espionage group COLDRIVER is adding the ClickFix attack method to its arsenal. The Zscaler ...

A new wave of macOS attacks is targeting developers via fake download websites that look like legitimate plat...

North Korean threat actor UNC5342 is using a new technique to spread malware via public blockchains: EtherHid...
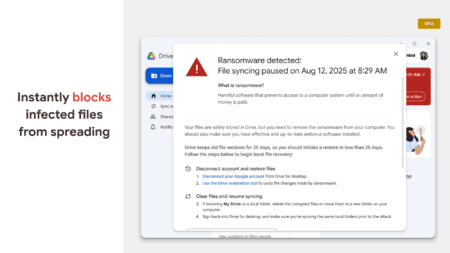
Google introduces AI-powered ransomware detection in Drive for desktop. The system automatically pauses file ...

A malware infection in postmark-mcp, a popular MCP server with 1,500 weekly downloads, highlights the lack of...
Endpoint security tools protect users against compromises. However, EDR-Freeze disables them via error messag...

A cyber attacker installed the Huntress endpoint security solution to protect himself. What he didn't realize...
The first "fileless worm" on the internet plagued organizations in 2001. A new report from LevelBlue shines a...