Okta recently hosted customers at the FC Utrecht stadium in the Netherlands. This MeetUp focused on ‘The Converged Identity Approach’. What exactly does that entail?
Identity has evolved into a broad concept, continuously leading to new solutions. Extra solutions can cause headaches, such as when access to internal data is managed independently of monitoring the IT environment. This leads to unnecessary blind spots, too much manual maintenance, and additional costs. In short, identity needs to be a platform. That’s the convergence Okta is referring to. IAM (identity & access management), IGA (identity governance & administration) and PAM (privileged access management) belong together, according to the company. At Okta, that translates to a ‘single pane of glass’ dashboard that many other IT companies are now discussing.
Okta Customer Identity Cloud and Workforce Identity Cloud have different management environments, but both include a dashboard to capture all identity tools at a glance. These platforms offer products such as Single Sign On, Universal Login, Lifecycle Management and Workflows. Those components can be chosen separately but naturally complement each other.
Incidentally, it is not just Okta itself that notes that identity must be treated holistically. Gartner predicts that 70 percent of all identity & access management solutions will be “converged” by 2025. The increasing complexity of IT environments means that managing as many identity issues on your own is no longer feasible.
The right balance
Martijn Morshuis, Senior Solutions Engineer at Okta, explained at the event that a unified identity platform is the linchpin of security. There are several reasons for this, aside from the obvious. One is that a single, centralized identity application prevents frustration. Employees are not waiting for constant authentication requirements. The only time you, as a user, are consciously concerned with access management is when it creates a roadblock that appears unnecessary.
The central role of identity also means that employees in different departments have to actively engage with it. For example, a product manager may find themselves asking the IT department to manage file access, which is a cluttered approach and, above all, slow. Such agency must be integrated with the teams that deal with it.
Having learned that lesson, it forms the basis for Okta’s vision for identity and access management (IAM). It must protect resources while providing the best user experience at the same time. In doing so, multifactor authentication (MFA) basics aren’t enough. For that reason, Okta’s products integrate seamlessly with known standards. On Apple devices, that means support for Touch ID; on Windows, it applies to Windows Hello for Business.
Identity Threat Protection
Without continually asking for a password, passphrase or fingerprint, Okta keeps an eye on things via its own data and that of other platforms. It does so through its new Identity Threat Protection. We discussed it back in October last year at the company’s Oktane event in Las Vegas. Thanks in part to Okta’s own AI, this feature offers the ability to ensure continuous security. One of its main uses is preventing sessions from being hijacked, as signals of this by Okta can, for example, force a new biometric check.
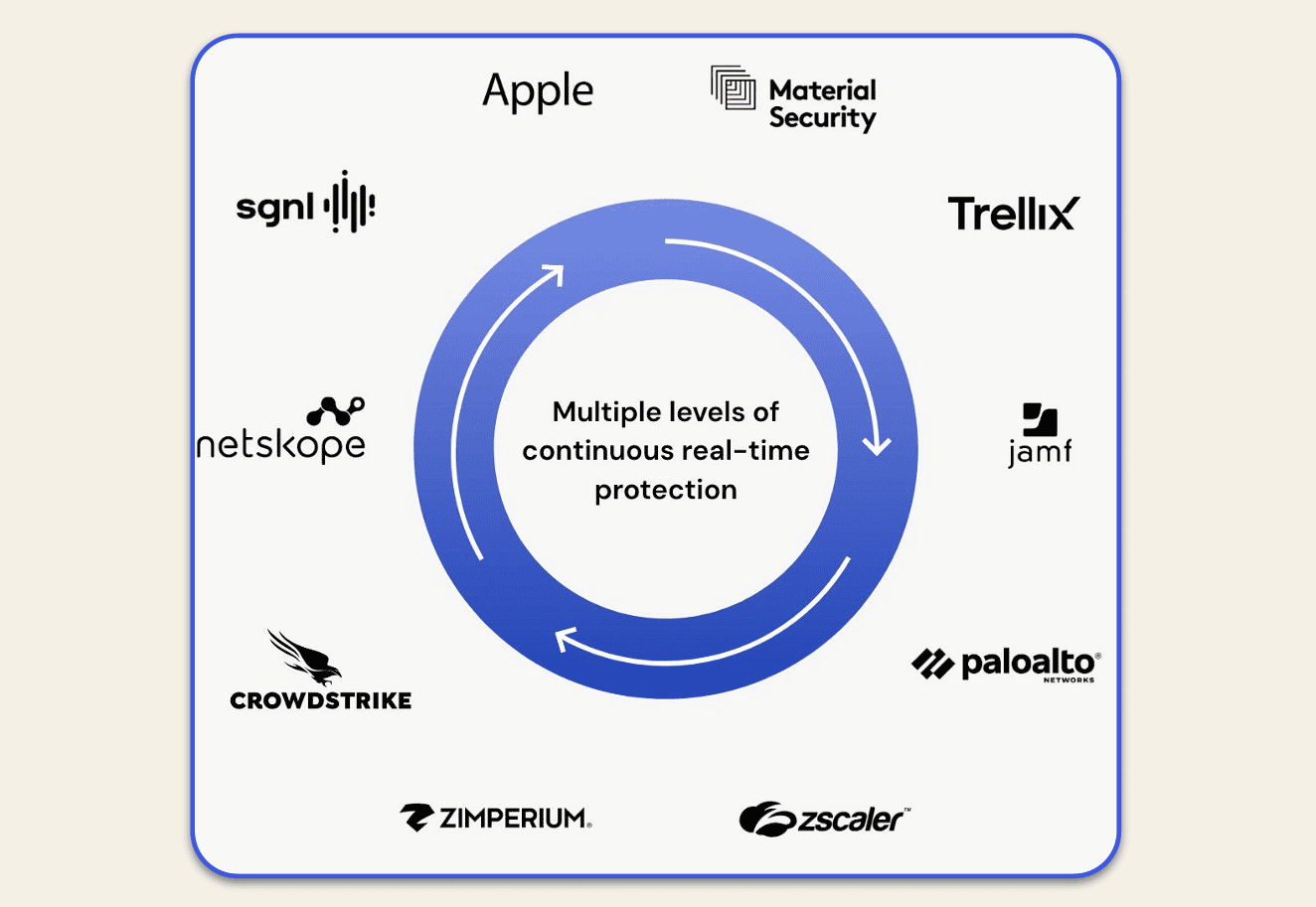
Integrations are arranged through the Shared Signals Pipeline, set up by the OpenID Foundation. Real-time protection, therefore, takes place using partners such as Palo Alto, CrowdStrike, Zscaler, Trellix and more (see below).
Since these integrations rely on open standards, other identity players would naturally like to jump on board. However, if you follow Okta’s reasoning, that still leads to an unnecessary split of identity. Convergence is thus the magic word at Okta.
Identity Governance
Identity governance (IGA) makes that convergence of identity much clearer. Morshuis explains that discrete IGA solutions can take 12 to 18 months to implement. In addition, he says, they are frustrating to work with, leaving user adoption lagging. Morshuis promises that Okta customers can take care of IGA within a few weeks.
This means that IGA, or arranging visibility, role allocation, and risk management, is easy to manage. For example, complex identity issues can be managed through Workflows, the no-code platform within the Okta suite. Any public API can connect to it, so this management layer covers all kinds of services.
So, no IT teams are needed to determine access constantly. Business users are at the controls themselves. Fine-grained authorizations remain accessible through Entitlement Management, integrated with the other Okta solutions Access Request and Access Certification.
Privileged Access Management
The final piece of the identity puzzle involves Privileged Access Management (PAM), which involves managing access to critical resources and accounts. Through PAM, admins can choose whether or not to allow other users to share certain privileges, for example. Morshuis concludes that the cloud continuously increases the importance of this. New apps, accounts, and workspaces make identity management more complex than ever. Often, the blind spot is service accounts: these are used irregularly and sparsely, making them easy to overlook.
Those switching to Okta from a legacy identity solution (read: managing access manually) can overcome such problems. With PAM, unused legacy accounts can be eliminated. Organizations ideally choose a closed infrastructure, with the principle of least privilege at its core. Combined with password rotation, this provides a secure and orderly IT environment that can be managed through a single solution.
Practical example: Bynder
Let’s take a practical example to find out how this works out in reality for organizations. Bynder focuses on digital asset management and has been an Okta customer for six years. Bynder’s promise is that organizations can access their logos, press materials, and other files, anytime and anywhere. Manager of IT Ops & Architecture Leotrim Dani says Okta makes this process secure and easy. The integration with Touch ID allows a PR manager with an iPhone to log in at lightning speed to access the company logo once the device is approved.
Bynder realized five years ago that two-step verification was not enough. Okta FastPass, marketed as a “phishing-resistant MFA,” took the company further. It allowed customers to trust that context was included to authenticate users. Is an office worker suddenly logging in via Malaysia, or are there signs of a VPN when they normally never use it? Okta picks this up so that the appropriate accounts are notified of this activity.
Dani also points out that the Bynder customer base has steep security requirements. Through audits, his company must prove that data is kept secure and access is customizable. Because Okta logs much more than just logging in and out, it is possible to look back up to 90 days to see how access was arranged, what authentication was used, and through which accounts.
With a growing number of customers and more and more features, Bynder continually has more requirements for Okta. “To compete, you have to have a SaaS solution,” Dani knows. An overarching Software-as-a-Service solution that interprets identity broadly avoids having to tie all applications together or handle things yourself. Dani strongly advises against the latter: any custom solution is gone at Bynder; it only uses Okta to access all applications.
Read also: What is ‘credential stuffing’ and how do you defend against it?