CrowdStrike is a provider of cloud-native endpoint security and is purely focused on B2B. Since 2011 the American company has grown explosively. We spoke with Ronald Pool, Cyber Security Specialist at CrowdStrike, and got a glimpse of what the company is doing. Not only does CrowdStrike focus on endpoint security, but threat intelligence and incident response for affected organisations are also a high priority.
The founders of CrowdStrike found that their former employers did not fully understand their vision of modern security techniques, so they decided to take matters into their own hands. The main goals at the start of the company were to use fewer agents at endpoints and to simplify the security of an entire company as a holistic entity. This means less delay, fewer conflicts between agents, and with the help of a cloud-native approach, this is possible with CrowdStrike’s solutions.
At CrowdStrike, you can not only rely on the daily cyber protection of your company or organisation. The company also offers possibilities to learn more about the threat actors that may have targeted your company. And if a breach does occur, CrowdStrike believes it is better to hang up on the phone as soon as possible, so they can tell you what the best action plan is. Below we will zoom in on these services in more detail.
Endpoint
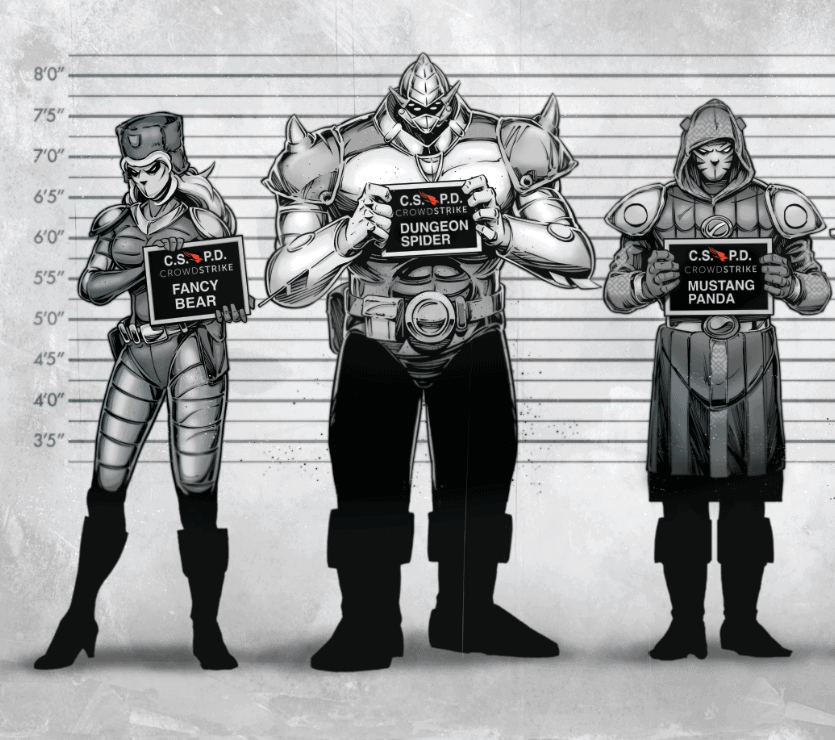
There is, of course, the CrowdStrike endpoint solution. A solution that keeps track of everything on a system: which registry entry is addressed, which files are touched, what does each process do at a certain moment, and what communication takes place with the internet? All this information is then also matched with intelligence from the threats that are monitored by CrowdStrike. If, for example, any behaviour is spotted that corresponds with the Russian hacking group Fancy Bear (also known as APT 28, Pawn Storm, Sofacy Group), you as an organisation know that the threat in question must be given a high priority. CrowdStrike’s endpoint solution works closely with their threat intelligence.
Threat intelligence
In a press release which we received a few days before CrowdStrike’s interview, the company reported that Chinese hackers are now as active as Russian, Iranian, Vietnamese and North Korean hackers combined. According to Pool, that’s a pretty significant wave. At the time of our interview, CrowdStrike was tracking some 120 threat actors. Previously, Russian hackers were much more active, mainly due to political motivations; often at times around elections. According to Pool, today’s geopolitical situation plays a major role in the activities of nation-state actors. Chinese hackers are now most busy with intellectual property theft. In other words, acquiring knowledge about certain technologies. In concrete terms, Pool gives an example of a design for a new Chinese aircraft in which one component was stolen from one vendor, another component from another, and yet another component came from a third party’s database. With the current trade war between the U.S. and China in the background, the rise in that type of attacks from China may not come as a surprise, but as a company, it is useful to be prepared.
CrowdStrike, like many other security companies, makes the distinction between the aforementioned nation-state actors and e-crime. E-crime is a threat to every company; these are threat actors called spiders by CrowdStrike, and they are purely concerned with financial gain, which in the majority of cases amounts to ransomware in all kinds of forms. Targeted ransomware, in which a particular organisation is selected by hackers who then suddenly shut down the entire company, is also part of this. What CrowdStrike can do for companies in this respect is to recognise certain methods and tools of hackers.
Tools, techniques, procedures (TTP)
Pool says that, in the past, nation state actors had tools at their disposal that e-crime actors could only dream of. Slowly but surely, therefore, attribution became easier. In other words, the use of a certain tool often meant that there was a certain hacker group behind the attack. Of course, that’s not what nation-state hackers want, which led to them sharing more tools. According to Pool, some tools remain exclusively available to nation-state actors. Stuxnet is a good example of this, according to him, because it used four different zero-day exploits. These are scarce to find at all, but four different exploits at the same time were quite exceptional. However, nation-state actors themselves began to make more use of generally available tools, including the Metasploit pen-testing service. In order not to be detected themselves, hackers use advanced tools such as tactics. From the “bad guys” point of view, this is, of course, a win-win.
However, it is often the case that many companies do not realise at all that they are a potential target. According to Pool, all organisations where certain knowledge can be obtained, or organisations where knowledge is created (e.g. think tanks and the like) are a potential target. CrowdStrike, therefore, has many people in the field who are active on the deep and dark web, to detect threats. In this way, reliable intel needs to be created from a variety of sources that companies can use proactively. For example, they can view reports or see in the CrowdStrike portal how a particular actor behaves, how it develops, and what its characteristics are. In this way, companies can arm themselves against threats based on information, if, for example, they suspect that they are being attacked by a certain actor.
Cloud-native approach
The emphasis on a cloud-native approach at CrowdStrike is mainly due to the nature of the endpoints, not all of which can nowadays be found in the company network. There are endpoints that are on the move, and there are endpoints that are sometimes connected and sometimes not. If a traditional solution is used, which therefore operates on-premise, a company already needs to set up something like a VPN to ensure that all the necessary data gets to where it is needed. Even with an enterprise query, where the entire company has to be searched, cloud-native is more advantageous. If an organisation receives signals that a certain hacker group may want to penetrate, such a broad query must be done to check if they are not already inside somewhere. However, if not all systems are online, this broad query is of no use. In the case of cloud-native security, the cloud can simply be searched, because it is, by definition, always connected.
Pool further states that it is much easier to stay up-to-date. With CrowdStrike’s system, groups can be set up: for example, one group of systems can always get the latest version, another group the penultimate, and yet another group of systems can always be updated manually. This way, less time is spent on updates because it can all be automated from the cloud.
This approach also works for customers who still use legacy technology. According to Pool, if CrowdStrike can communicate with the cloud, there is nothing wrong, as long as the technology is younger than Windows 7, service pack 1. Pool says that there are still some applications for Windows XP: “You still come across it sometimes, especially on the side of industrial technology. That OT (operational technology) sometimes is really old, but what you see is that attacks often go via the IT side to the OT side. So as long as you’re up-to-date around the OT, you can still see the attacks coming”.
Besides technical services also situational tests
CrowdStrike can also investigate for companies which actors are likely to threaten them. Subsequently, a simulation of an attack can be launched, which gives the opportunity to test how well an organisation is armed against it. This is done on a technical level, but also with regard to the decisiveness of management and employees. So if you, as a company, really want to be sure how you are doing when it comes to cybersecurity, CrowdStrike has methods for that.
Ronald Pool describes: “Do you detect a threat, and do you detect it in time, or will there be a panic? We do that kind of exercise at the technical level, but also at the management level. Then we sit down with all the stakeholders and do an exercise. Suppose the company now receives a phone call from a random media outlet, saying that in three hours’ time, an article will go live that says they’ve been hacked. Is everyone going to do what’s really good for the company, or do you see a flash of blind panic and people running to a closet to dust off an old book with emergency procedures in case something goes wrong? That kind of exercise can be very confronting for companies.”
In short, CrowdStrike has a portfolio that is intended to offer companies a less complex security approach, but also to make companies aware of what is actually coming at them. As far as we are concerned, the cloud-native approach is future-proof, and the incident response services the company offers are a convenient way for companies to test themselves. We are, therefore, very curious to see how CrowdStrike will grow.
