For many businesses, realising the right security strategy is a puzzle that never gets finished. It is often assumed that you first need to address your application layer before you can start looking at the data policy. “It is a complete approach that secures your business”, states Micro Focus. The security solution provider acknowledges applications should be a priority, but the right data security approach is perhaps just as important.
Micro Focus has a broad portfolio to support the security strategy of companies. Through its talks with clients, it knows the common problems. These are particular issues, but also inefficient approaches that regularly occur. The importance of applications, data and identities is not always properly prioritised.
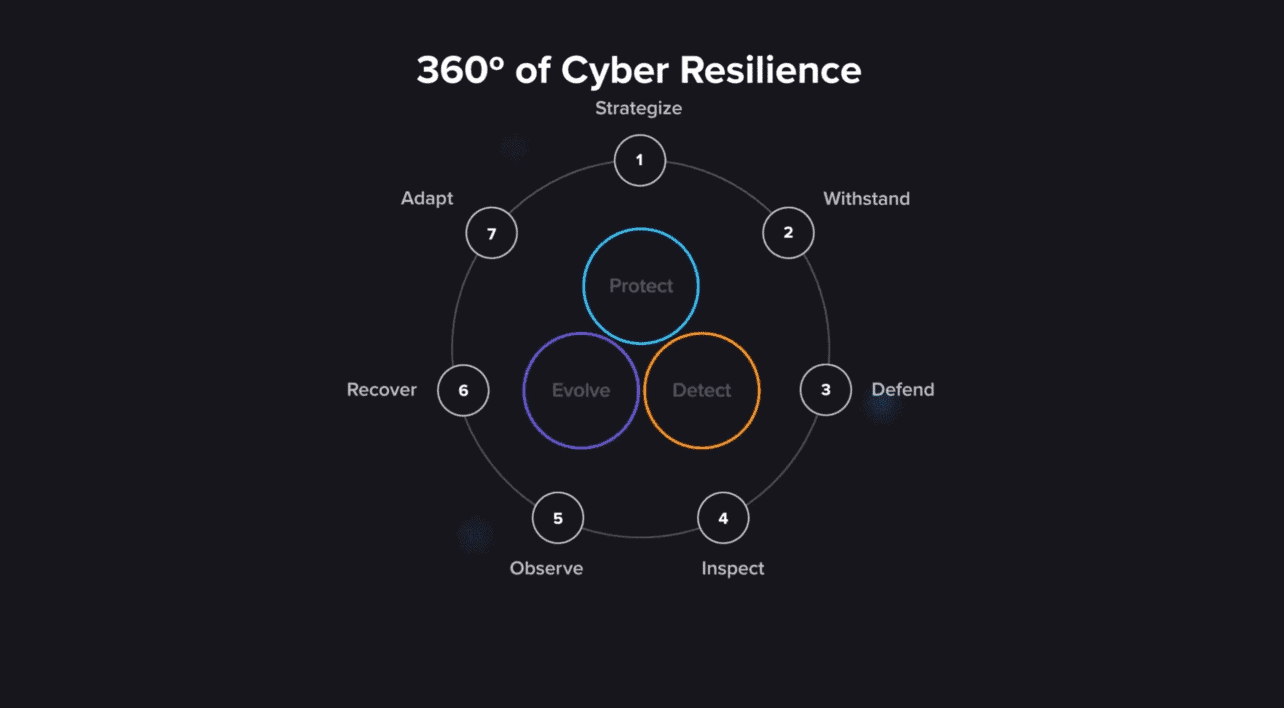
As a company, it is therefore best to adopt a ‘cyber resilience‘ approach. This approach takes into account the aspects that are common to every modern business: applications, user roles and data. It involves developing an application, testing the code and making sure the application can withstand attacks. It also involves looking at who is going to use the application and who should have access to it. What every application also has in common is that it generates and/or consumes data.
Tip: Software testing: nobody questions the need, but it’s not done enough
“However, companies do not always have a clear picture of what kind of data is being generated, whether that data is being generated in the right way and if the data might end up in places where it can cause damage,” says Micro Focus Pre Sales Consultant Chris Winter. This is the core of the problem Winter often sees. And so it is time to keep data, just like applications, continuously high on the priority list of the chief information security officer (CISO).
Discover, analyse and remediate
To gain insight into data and the risks associated with this, companies can take several steps. First, awareness is needed that not all data is the same. For example, there is unstructured data that comes from text, video and audio. This type of data can be generated during a virtual meeting at a financial services company, where sensitive information about upcoming transactions is shared via a video conferencing service. There is also application data generated by software such as Customer Relationship Management (CRM) and Enterprise Resource Planning (ERP). Such data often resides in a database and is usually organised.
When it is clear whether unstructured data or structured data requires extra attention, targeted solutions can be deployed. The Micro Focus products are focused on both structured and unstructured data. The solutions can be used, among other things, to run discovery processes, but also to move data by means of policies or to protect it by means of encryption. Perhaps there is a great need to visualise and discover the data of your business? Or do you have a need for applying encryption and/or moving and deleting data? Micro Focus can help you with this.
What does it look like, exactly?
If we take a closer look, it seems that discovery solutions are in particular useful for building good security policies. Users get insight into all data sources within the company. This makes it possible to see what is going on through a dashboard. This is useful for studying large data sets, but also for analysing data points in detail. These discovery possibilities do differ per type of data. With video and audio conversations, for example, you can build a complete index of what is being said. With databases, however, data discovery is applied more to searching for privacy-related information, such as telephone numbers and e-mail addresses. In the end the discovery tools excel in their versatility: from looking at the location and status of sensitive data, to determining how to clean your databases, to implementing a good General Data Protection Regulation (GDPR) policy.
For companies that want to take their data policy a step further, there are also encryption and protection solutions with Micro Focus Voltage. With this software, your company’s encryption policy and security policies can be put into practice. For example, financial services and government organisations choose such a reinforced policy because they have very sensitive information stored in their databases. They then apply strict encryption configurations to it.

Although on the discovery and remediation side these are separate products, Micro Focus can of course offer benefits to companies that purchase multiple products. Users going through discovery processes from the Structured Data Management solution may at some point come to the conclusion that they want a data set encrypted. By passing this data set entirety to the Voltage solution, a mask is automatically placed over it. Encryption is then performed as quickly as possible, regardless of the location.
Ultimately, Micro Focus believes very strongly in these targeted solutions. It wants to use strong products to solve the problems that businesses face. This way, it can become a one-stop-shop partner for companies, but also exclusively address very specific problems. Companies sometimes only come to Micro Focus to use its services for moving data between environments and placing that data in a secure vault. Such customers may buy more products over time, because of their first experiences with Micro Focus. According to Winter, customers also really see the value of such a broad approach with targeted solutions, as they meet the exact requirements of the end-user. Subsequently, the strong underlying integrations will make the integral approach a success.
Solutions rely on developed engines
Businesses that turn to Micro Focus for various solutions can also benefit from the cooperation of the underlying engines. The more Micro Focus solutions businesses use, the more data flows through those engines. This also means that the engines can extract more value from that data. Micro Focus uses these engines:
- Intelligent Data Operating Layer (IDOL) – makes data searchable and understandable. It can be used, for example, for discovery and recognising and tracking faces in video files.
- Vertica – mainly the engine behind Micro Focus’ Business Intelligence (BI) and analytics applications. Used to a lesser extent for security solutions.
- User Behaviour Analytics – software that analyses many logs to determine expected behaviour and detect deviations.
IDOL is widely used in the security field for the data discovery issues mentioned earlier. This can include automated data classification, file indexing and detecting sensitive information in videos.
We see insider threats popping up more and more often.
The User Behaviour Analytics engine, on the other hand, is more suitable for Security Information and Event Management (SIEM) applications. It retrieves a lot of information by reading logs, anonymously wherever possible, of course. This should reveal how employees and the company behave. For example, it looks for deviations based on role access and working hours. If several deviations are found, the engine signals a behaviour change. The security operator and solutions must then be triggered immediately because it could indicate a hacked account or an insider threat. Especially now that such threats are becoming more common, support of this engine can come in handy. “The insider threat is a theme that we see coming up more and more often these days,” says Winter.
Unique situations require targeted approaches
According to Winter, it is best to discuss your company’s security strategy with a partner such as Micro Focus, as this can lead to a targeted plan. Winter mentions an example of a somewhat smaller company that lost intellectual property to a departing employee. In this situation, using the Behaviour Analytics engine seems logical at first, as it prevents such insider threats. However, the company did not know exactly what was happening with its data and how it was being stored. After analysing the situation, they started a discovery process to see where all the data is located and where the risks lie. Almost half of the used storage capacity could be cleared, either because of duplication or because it was redundant data. All relevant data that remained was then placed in a safer location.
Such an example shows that the obvious solutions are not always the right ones. It also shows the need for a good information management strategy. Not every company has this strategy in place and high on their priority list. However, securing data is perhaps just as important as secure applications. By working on the security of all those assets, companies can keep many cyber threats at bay. And so the whole business becomes stronger.