Cisco expands integration between networking portfolios also in the area of secure access.
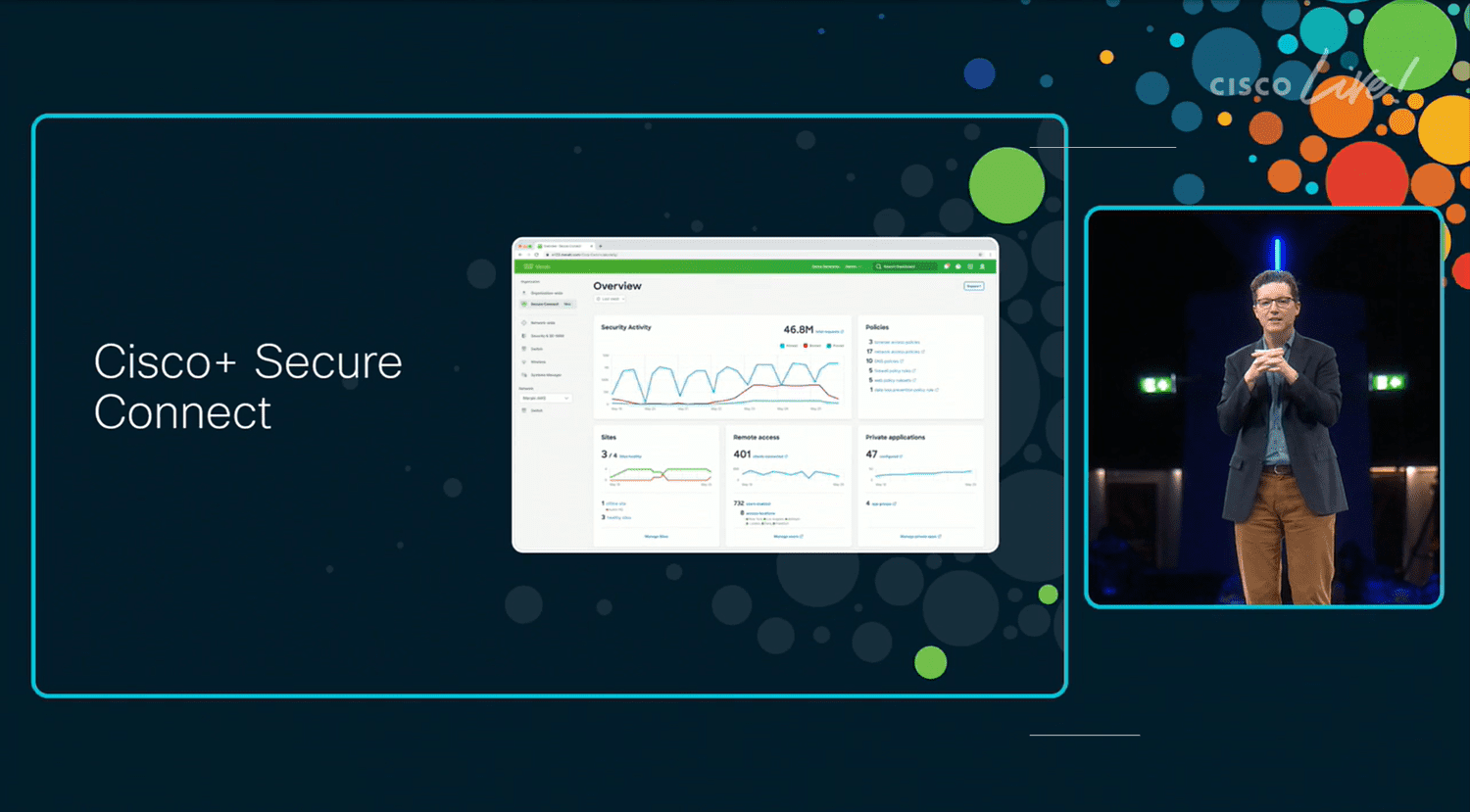
Last year at Cisco Live, there was quite a bit of focus on Cisco+ Secure Connect. This SASE service should ensure secure access to enterprise networks, cloud environments and SaaS solutions from anywhere. There was also the announcement that Cisco is going to merge its Catalyst and Meraki portfolio offerings. This means Catalyst hardware can also be managed from Meraki’s cloud-managed environment.
First Meraki SD-WAN, now also Viptela
This year at Cisco Live EMEA in Amsterdam, Cisco is making an announcement that could be seen as another step in the ever-increasing integration within its offerings.
SASE is basically an amalgamation of SSE (being able to securely connect) and SD-WAN (optimally distributing traffic). Cisco+ Secure Connect is undoubtedly a SASE product, yet it also had a limitation. When introduced, it was essentially a product from the Meraki stable. That meant it only had support for Meraki SD-WAN built in. As of now, that is no longer the case. Cisco announces that it now includes support for Viptela (officially called Cisco SD-WAN powered by Viptela) within Cisco+ Secure Connect.
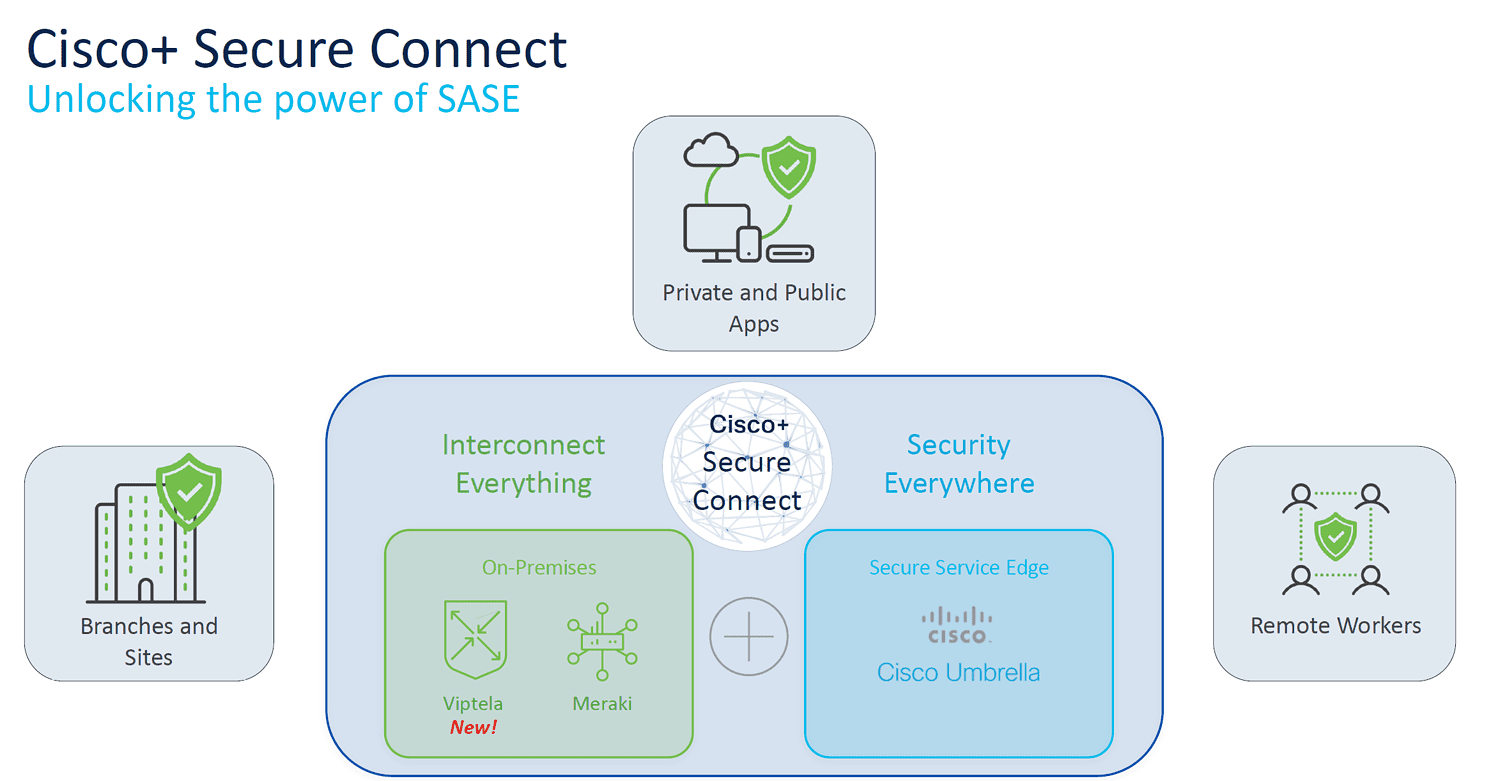
With this announcement, Cisco is taking quite an important step. It ties the world in which Catalyst operates a bit more into the world of Meraki. Whereas Meraki has traditionally focused on SMEs (Small and Medium Enterprises), Catalyst focuses more on LEs (Large Enterprises). The same is true of Meraki SD-WAN and Viptela. In a nutshell, Viptela focuses on a more complex (hybrid) environments than Meraki SD-WAN.
The above implies that Cisco+ Secure Connect as it was until today was not really interesting as a SASE solution for large enterprise, which is most likely to go for Viptela rather than Meraki SD-WAN. With this integration, Cisco is closing that gap. Cisco+ Secure Connect is now a solution that could theoretically be of interest to the entire enterprise market.
Much emphasis on risk
In addition to the expansion of Cisco+ Secure Connect, Cisco also has some other announcements in store today in the area of security. These mainly involve recognizing risk. For example, new features are available within Duo Risk-Based Authentication. These are mainly aimed at creating less friction with users, without compromising on security.
An example of this is what Cisco itself calls Remembered Devices. Combined with Wi-Fi Fingerprint (determining risk based on the fingerprint of SSIDs in the vicinity), this allows users to stay logged in longer as they use familiar applications, devices and networks. The interesting thing about this is that Cisco claims it can do this without collecting personal or location data.
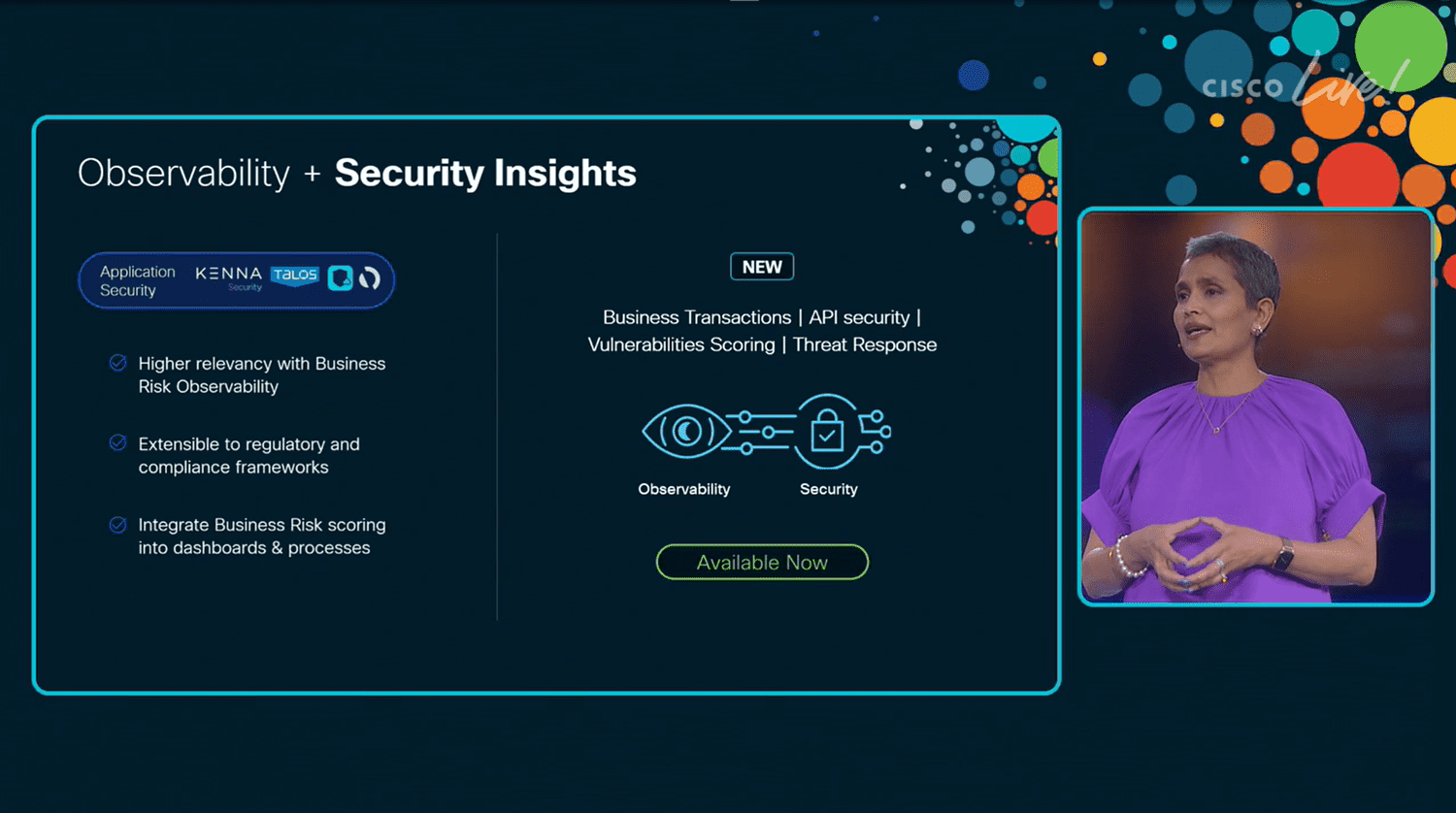
Finally, there is Business Risk Observability. This is primarily about application security. According to Cisco’s own new Cybersecurity Readiness Index, organizations are not doing well at all in this area. Only 12 percent claim to have covered this properly. This is why Business Risk Observability will be available as an extension to Cisco’s full-stack observability offering (more on this in a separate story). It is part of Cisco Secure Application, which in turn is integrated into Cisco AppDynamics, and provides a score based on multiple components, including the Kenna Risk Meter score. It also has integration with Panoptica for API security and, of course, the overarching Talos, for threat intelligence. In this way, organizations should get faster and better insight into how secure their applications (and their APIs) are.
Also read: Cisco builds open and integrated security platform