The WIP26 malware uses public cloud environments to launch attacks against telecom operators. The malware tries to appear as legitimate.
These findings come out of research by SentinelOne. The WIP26 malware targets spying activities. Telecom operators in the Middle East are particularly affected by the new malware, SentinelOne concludes in its analysis.
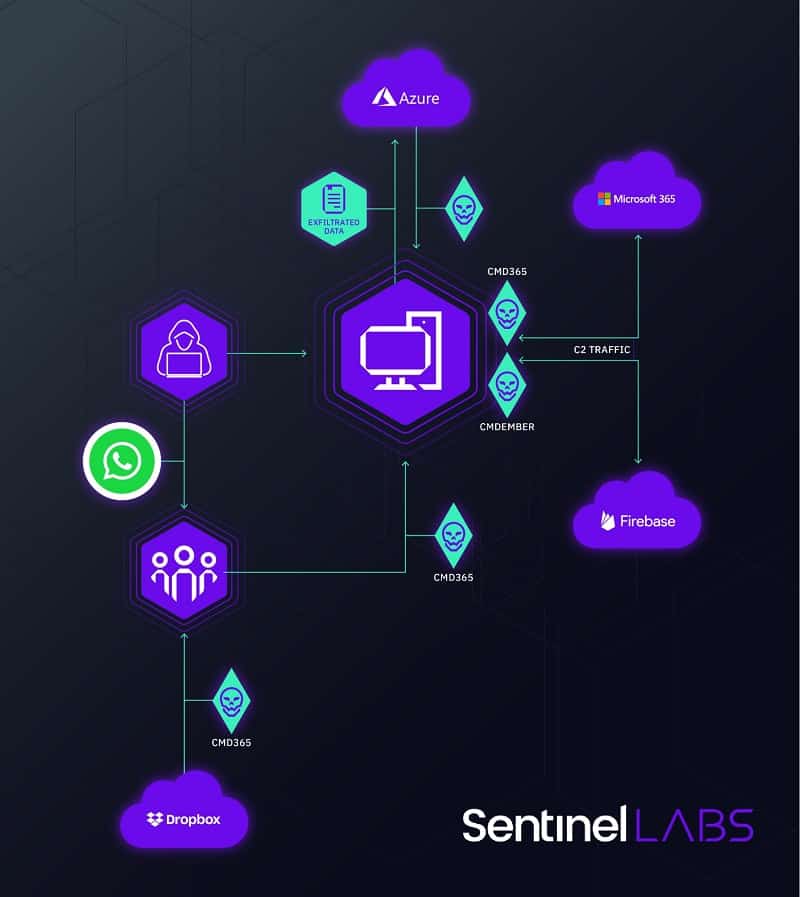
Interestingly, the new malware likes to use public cloud environments to come across as legitimate software or operations. The malware uses Microsoft 365 Mail, Microsoft Azure, Google Firebase and Dropbox to deliver malware and data exfiltration.
More specifically, the attackers use the CMD365 and CMDEmber backdoors to attack the Microsoft 365 Mail and Google Firebase services for this purpose. This is to exploit them for C2 servers. In addition, Microsoft Azure and Dropbox instances are used for data exfiltration and hosting malware.
Attack process
SentinelOne was also able to map the attack process. A WIP26 attack starts with enticing employees of the telecom networks via WhatsApp to install a malware loader.
Then the backdoors in question pretend to be utilities, such as a PDF editor, a browser or software that performs updates. Including associated legitimate file names, icons and digital signatures. This masks the ultimately malicious C2 traffic and makes it difficult to detect this malicious traffic.
Mistakes made by cybercriminals
Exactly who is behind the malware attacks on telecom providers is not known. Since telecom operators have been attacked, it does appear to involve spying activities, so the attacks may be attributable to state-sponsored APT groups, although in this case it is not certain.
According to SentinelOne, the cybercriminals made some OPSEC errors that do not normally occur in real APT attacks. For example, the JSON file in which the Google Firebase C2 server stores data is publicly available. This provides more insight into WIP26. SentinelOne therefore continues to monitor WIP26 to gain more insight into the development of this advanced malware attack.
Also read: WIP19 malware threatens IT service providers and telecom companies