A data breach at Nvidia allows cybercriminals to disguise malware with trusted code signing certificates.
Since last week, ransomware group Lapsus$ claims to possess over 1TB of private Nvidia data. Although Nvidia acknowledges that data was stolen, the organization “expected no impact on customers”. That appears to be an error in judgment. Cybercriminals are actively using stolen code signing certificates to spread malware on Windows PCs.
A code signing certificate allows a developer to sign files. The signature informs Windows of a file’s origin and modifications. End users and third-party apps can reject applications based on a signature.
Stolen signatures are an excellent means of disguising malware. Currently, code signing certificates from Nvidia are being used to obfuscate multiple forms of malware, including Mimikatz and malicious Cobalt Strike beacons.
Defence
Signatures have an expiration date. Although the stolen signatures in question have already expired, signed applications will still be executed by Windows. Some security tools, including Windows Defender, allow you to create policies that block files with signatures from certain vendors and serial numbers. That’s the best defence for now. According to security researchers Kevin Beaumont and Will Dormann, all signatures use the serial numbers below.
Nvidia under pressure
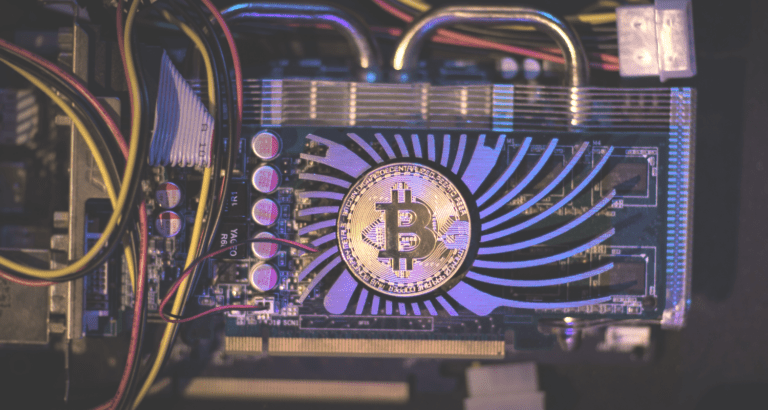
Lapsus$, the ransomware group mentioned before, leaked the code signing certificates to pressure Nvidia. The ransomware group is trying to force Nvidia to increase the Lite Hash Rate’s (LHR) of GPU’s. GPU’s with high LHRs are suitable for cryptomining. Nvidia is limiting the LHR of video cards to prevent cryptominers from buying up all its stock. Lapsus$ threatens to leak all stolen data if Nvidia continues to limit the LHR of video cards.