Security company Zscaler found three notorious malware variants in dozens of Google Play Store apps. The apps were downloaded more than 300,000 times in total.
Most users expect the Google Play Store to be safe. In reality, cybercriminals abuse the platform to spread malware. Researchers at Zscaler recently found three notorious malware variants in Google Play Store apps.
Joker, Facestealer and Coper
Joker is one of the most common malware programs for Android. The malware silently purchases subscriptions on an infected device. Victims pay sky-high fees for unwanted services. Zscaler found Joker in more than 50 Google Play Store apps. The apps have a combined total of 300,000 downloads.
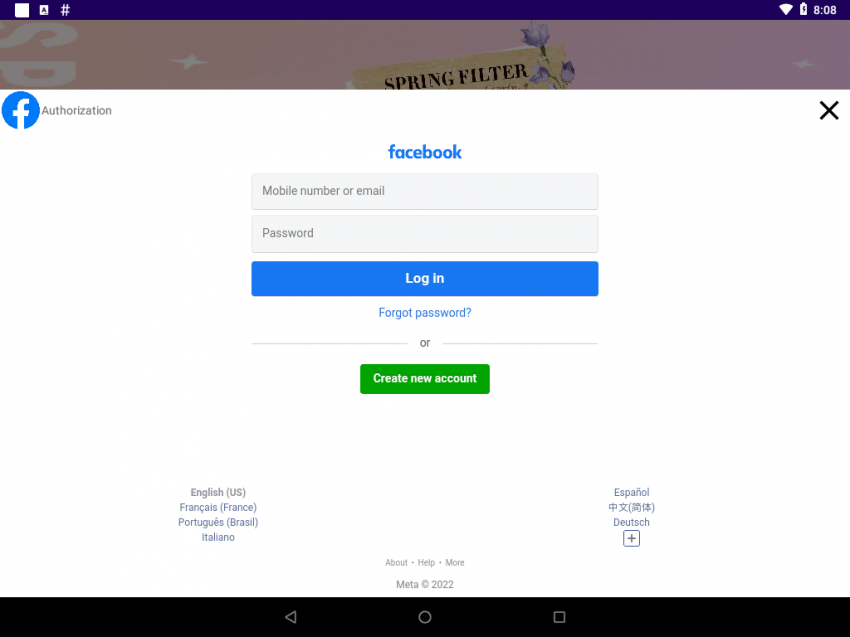
Facestealer is regularly spotted as well. Devices open a fake Facebook login page upon infection. The malware steals the login details that a user inputs. Zscaler found Facestealer in ‘Vanilla Camera’, a camera app with 5,000 downloads.
The third and final variant is Coper. This malware steals victims’ bank details by keylogging and intercepting SMS messages. Zscaler found Coper in ‘Unicc QR Scanner’, a malicious app that resembles a legitimate QR scanner.
Google’s role
The Google Play Store is supposed to bar malware. Google uses an automatic admission process to review apps. The apps that spread Joker, Facestealer and Coper use legitimate functions to bypass the admission process.
Google is aware of the problem. The tech giant will implement new app conditions on November 1, 2022. Although we expect the new system to recognize more malware, cybercriminals will undoubtedly find detours. Security research remains necessary. Zscaler informed Google about the apps found. Google since removed the apps.
Prevent
Zscaler advises end users to only download apps with high user numbers, positive reviews and trusted developers. The security company advises against granting accessibility rights to unknown apps. Malware apps often abuse accessibility rights to control infected devices.
Finally, Zscaler warns about messaging apps. Some messaging apps use the Read_SMS permission to read incoming messages. The permission allows a cybercriminal to intercept two-step verification codes on an infected device.
Tip: Popular apps for tracking children are extremely vulnerable
