The new security offering automatically turns on tamper protection and other features.
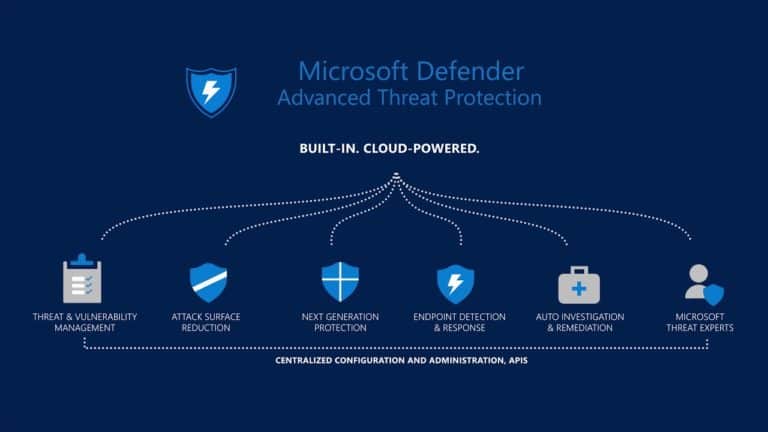
This week Microsoft announced new built-in protection features for all devices onboarded to Defender for Endpoint, its security platform for endpoint devices. Once applied, the new default set of settings provides better protection for enterprise endpoints against advanced and emerging threats, including ransomware attacks, the company said.
Built-in protection is a set of default settings that are rolling out to help ensure device security. The default settings are designed to protect devices from ransomware and other threats. Initially, built-in protection will include tamper protection for tenants, with other default settings coming soon.
Tamper protection
“Tamper protection in Microsoft Defender for Endpoint protects your organization from unwanted changes to your security settings”, explained Josh Bregman, Principal Product Manager at Microsoft.
“Tamper protection helps prevent unauthorized users and malicious actors from turning off threat protection features, such as antivirus protection. Tamper protection also includes the detection of, and response to, tampering attempts.”
Microsoft will be sending alerts to any customers who have not yet added tamper protection to their enterprise environments. Customers will get a Microsoft 365 Defender portal notification telling them the feature will be turned on.
“Tamper protection will be turned on for your tenant, and will be applied to your organization’s Windows devices”, Microsoft described on its support portal, adding that “whenever new devices are onboarded to Defender for Endpoint, built-in protection settings will be applied to any new devices running Windows.”
Corelight Zeek
Microsoft also partnered with Corelight to integrate its Zeek security solution into Defender Endpoint. Zeek is a powerful open-source network analysis engine that allows researchers to more effectively handle sophisticated network-based attacks.
Elad Solomon, Senior Software Engineer at Microsoft, described the new Zeek offering in a blog post. “The integration of Zeek into Microsoft Defender for Endpoint provides new levels of network analysis capabilities based on deep inspection of network traffic powered by Zeek.”
Solomon added that administrators onboarding endpoints to Defender for Endpoint can now monitor inbound and outbound traffic with Zeek’s engine.